Why Become a Business Analyst in 2026: Top Reasons and Scope
Thu, 18 April 2024

Follow the stories of academics and their research expeditions

How Did Capital One Respond to Their Major Cyber Incident?
In 2019, Capital One suffered its worst public data breach, showing stolen information of at least 100 million+ people. The cascading nature of this cyber incident runs through the financial space, infecting compliance fears that are disinfecting organizations from scrubbing their cybersecurity frameworks.
A masterful response that would be the blueprint of corporate crisis management in the digital era followed.A moment that changed the entire data conversation: when a big financial institution like Capital One found itself in surprise mode and responded.
A misconfigured web application firewall was exploited by an ex-AWS employee, and this is what led to the breach. A breach ensued, with confidential data like social security, bank details, and personal credit card applicants information leaked in this incident. Months later, Capital One uncovered the breach, a reminder to continuously secure your microservices and have threat intel.
Upon identifying the breach, Capital One acted immediately to minimize further damage. The company:
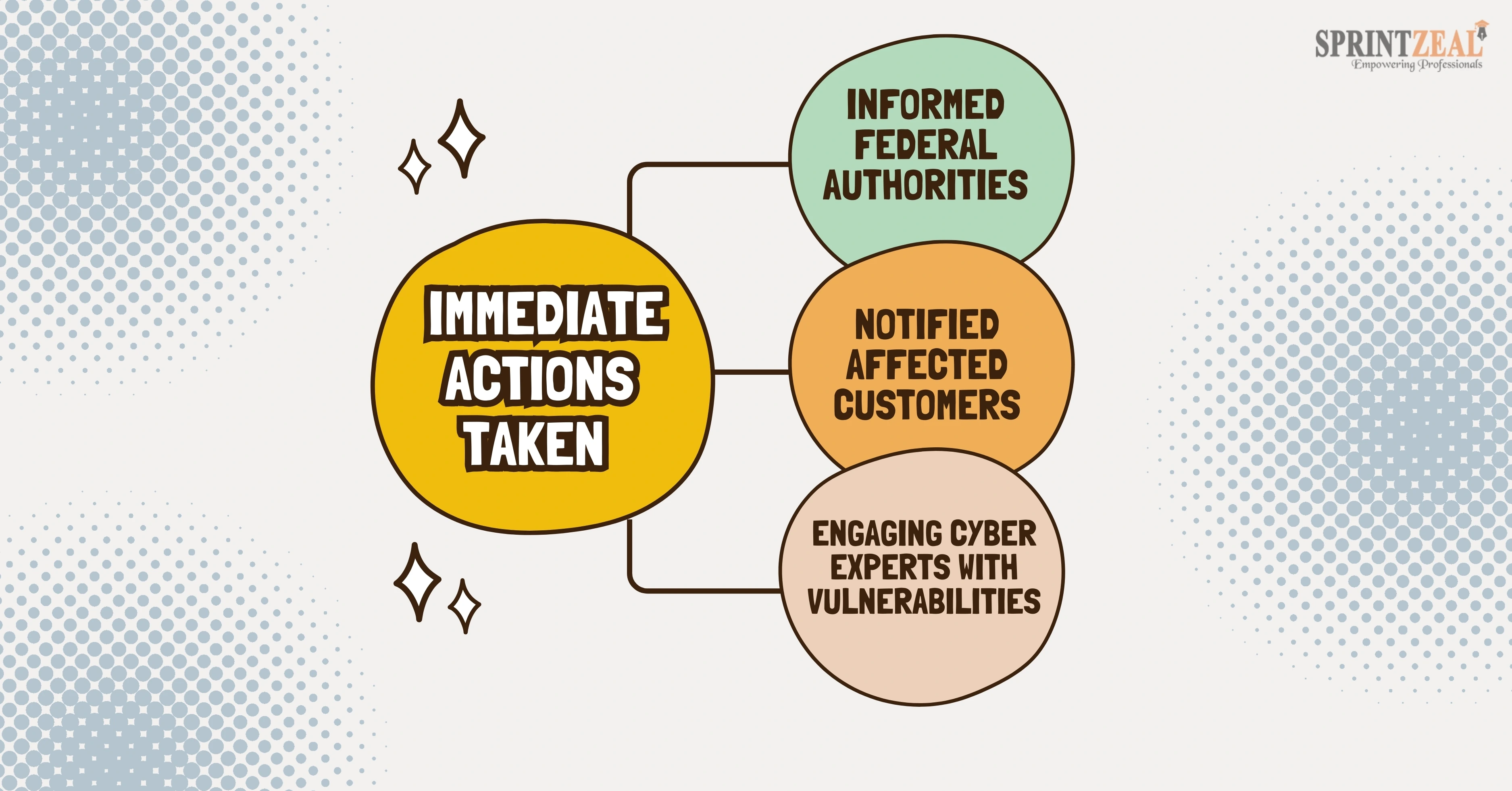
- Informed federal authorities and cooperated with the FBI to identify the culprit.
- NFC and Free Credit Monitoring for Notified Affected Customers
- Engaged cybersecurity experts to assess vulnerabilities and secure their systems.
Capital One made substantial investments in enhancing its cybersecurity posture. Some of the measures it has taken are:
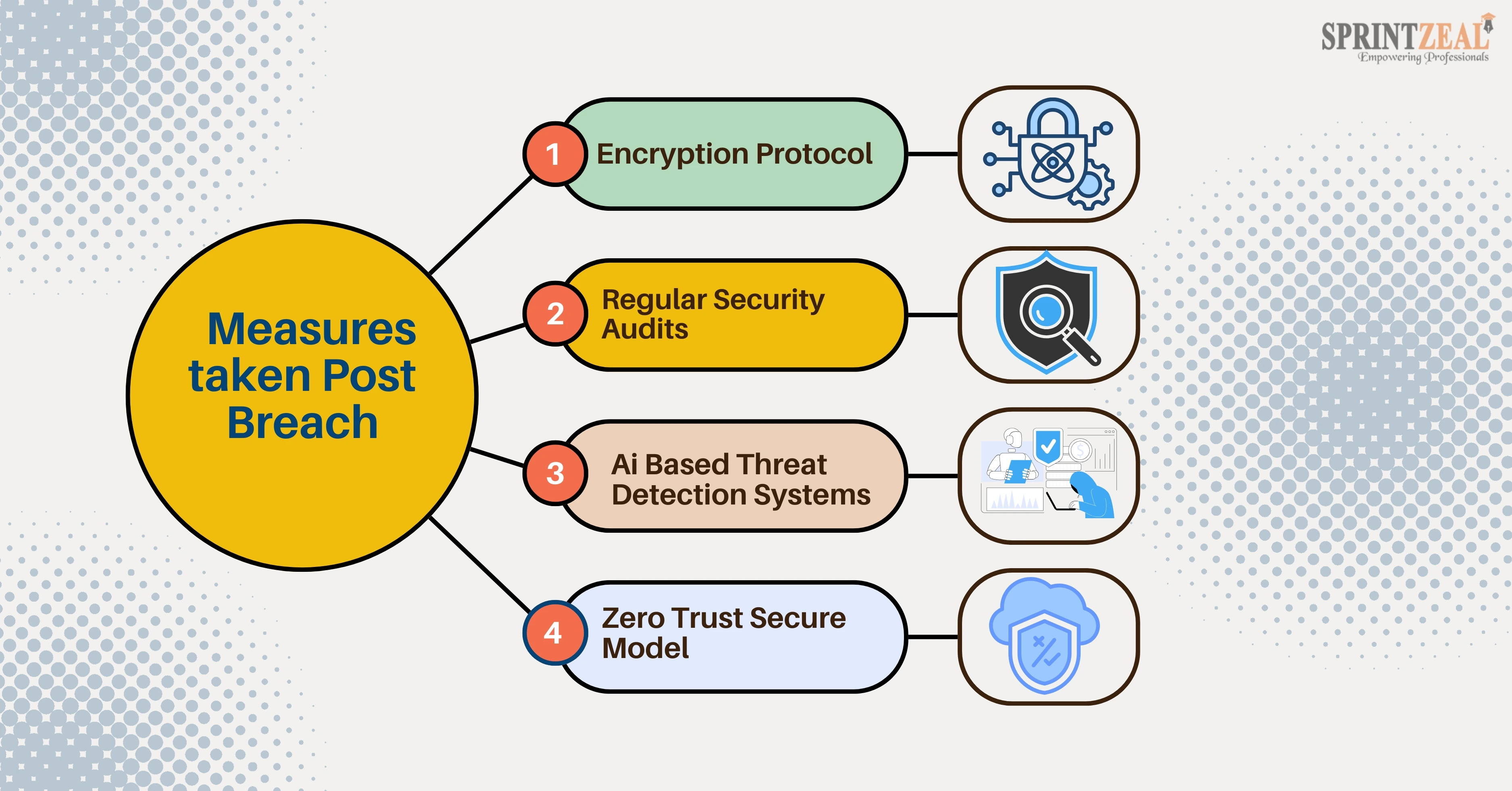
- Implementing stricter access controls and encryption protocols.
- Conducting regular security audits and penetration tests.
- Adopting advanced AI-based threat detection systems to prevent future incidents.
- Transitioning to a "zero trust" security model.
That breach resulted in large financial fines and an exam by several agencies. Capital One paid around a $190 million settlement to the customers who allege that they were harmed. The company was fined by regulatory agencies and suffered a reputational hit that frightened consumers. All these consequences brought more vigilance about the need for proactive cybersecurity spending.
You see, from the experience of Capital One, organizations learn some important things:
- Regularly monitor and audit system configurations to prevent vulnerabilities.
- Keep an incident response plan that will help you act fast in case of breach.
- Educate employees on best cybersecurity practices to avoid human error.
- During times of crises, maintain higher customer communication and transparency.
The Capital One data breach is a scary example of how the threat landscape is continually evolving in the present-day digital world. True, the breach has dire ramifications. Capital One's positive move followed by actions after the fact made the importance of being resilient and accountable very evident.
The clear takeaway for them is to prioritize cybersecurity data protection and trust in a hyper-connected future.
Consider Sprintzeal's Cybersecurity Training Solutions for all your needs and means of advancement in this domain. Contact our career experts to have your doubts clarified.
Q1: What led to the Capital One data breach?
The breach was caused by a misconfigured web application firewall that was leveraged by a former AWS employee, which resulted in unauthorized access.
Q2: What types of data were exposed in the breach?
The breach resulted in exposure of personal information like Social Security Number, bank account information, and other credit card users data as well.
Q3: How did Capital One respond to the breach?
Capital One informed federal authorities, informed affected customers through emails, offered credit monitoring services, and enhanced their cybersecurity measures.
Q4: What are the financial repercussions of the breach for Capital One?
Capital One agreed to a $190 million settlement for the affected customers and regulatory penalties, among other things.
Q5: What lessons can businesses learn from this incident?
Next, businesses ought to focus on their Cyber Shield Frameworks and embed periodic audits as well as real-time threat detection along with an efficient incident response plan.
Thu, 18 April 2024

Tue, 16 April 2024

Wed, 26 February 2025


© 2026 Sprintzeal Americas Inc. - All Rights Reserved.
Leave a comment