Why Become a Business Analyst in 2026: Top Reasons and Scope
Thu, 18 April 2024

Follow the stories of academics and their research expeditions

Organizations face a maze of delicate problems in safeguarding their IT ecosystems as they move more into the online world. The cybersecurity mesh, a groundbreaking framework created to offer security versatility in the modern, interconnected world, is presented. In a time when cloud computing, remote work, and connected technologies rule this same scene, existing security strategies based on a fixed boundary are no longer good. Through the devolution of security perimeters, cybersecurity mesh reinvents the concept of digital protection. It changes the emphasis from protecting a single boundary to protecting personal digital assets. This creative method is revolutionary in building strong organizational capacity against advanced cyberthreats because of its modular structure and connectivity.
The world in which advanced organizations work is one where interconnected networks and information choices are controlled. Businesses can operate safely and sustainably due to cybersecurity, which is the foundation of this ecosystem. The requirement of introducing security measures has indeed been spotlighted by the increasing complexities of cybersecurity threats like spyware, malware, and zero-day attacks.
Cybersecurity serves as a strategic enabling factor of trust instead of simply a protective shield. Clients, labourers, and other stakeholders rely on managers to support their data ethically. A single breach can have serious economic consequences, damage one's reputation, and lessen customer trust.
Cybersecurity mesh design enables a proactive, adaptable, and comprehensive security framework that assists organizations in effectively solving these problems.
Adopting the Cybersecurity Mesh Architecture (CSMA) offers distinct advantages, including enhanced scalability, flexibility, and integration across diverse systems. For organizations developing new infrastructures, it changes how network designs and security frameworks are structured. For those with existing systems, transitioning to this advanced strategy may require considerable changes initially, but the long-term data security and efficiency benefits outweigh the investment.
According to Gartner, CSMA comprises four key layers that provide the agility and adaptability needed to tackle the evolving challenges of modern security and network integration.
1) Security Analytics and Intelligence
At the heart of the cybersecurity mesh is centralized security analytics that enables real-time data collection, analysis, and reporting. This layer integrates data from various security tools and processes, offering advanced risk analysis, threat detection, and response capabilities. The continuous aggregation and analysis of data allow security teams to quickly identify emerging threats, reducing response times and minimizing the impact of attacks. CSMA enhances threat intelligence by delivering actionable insights and triggering automated responses, which strengthens overall defense mechanisms.
2) Distributed Identity Fabric
This layer focuses on decentralized identity management and offers features such as adaptive access control, directory services, and identity verification. It enables secure user authentication and access management across various platforms, especially in environments with hybrid or multi-cloud infrastructures. The distributed identity fabric ensures that identities are not confined to one system but are securely integrated across the entire network, providing seamless access while maintaining stringent security controls. This also helps mitigate risks associated with unauthorized access and enhances overall identity governance.
3) Consolidated Policy and Posture Management
The third layer of CSMA revolves around translating centralized security policies into native configurations for different security tools. It offers dynamic authorization services, allowing organizations to manage security settings consistently across various platforms and devices. This layer simplifies the enforcement of security standards, ensuring that compliance is maintained and reducing the chances of misconfigurations. By automating policy management, IT teams can more effectively identify vulnerabilities and misalignment with organizational security requirements, thus proactively addressing potential compliance issues.
Organizations often turn to cybersecurity policy templates to streamline policy management and ensure consistency across different platforms and security tools
4) Consolidated Dashboards
The structured dashboards given by CSMA give security situations and teams a single, cohesive picture of the whole, enabling them to react speedily to occurrences in different contexts. These dashboards offer real-time insights and enable more efficient decisions during threat intelligence by gathering data from various sources. It allows rapid threat-proof identity, speedier distribution of appropriate responses, and optimized incident management by combining data protection information into a data interface.
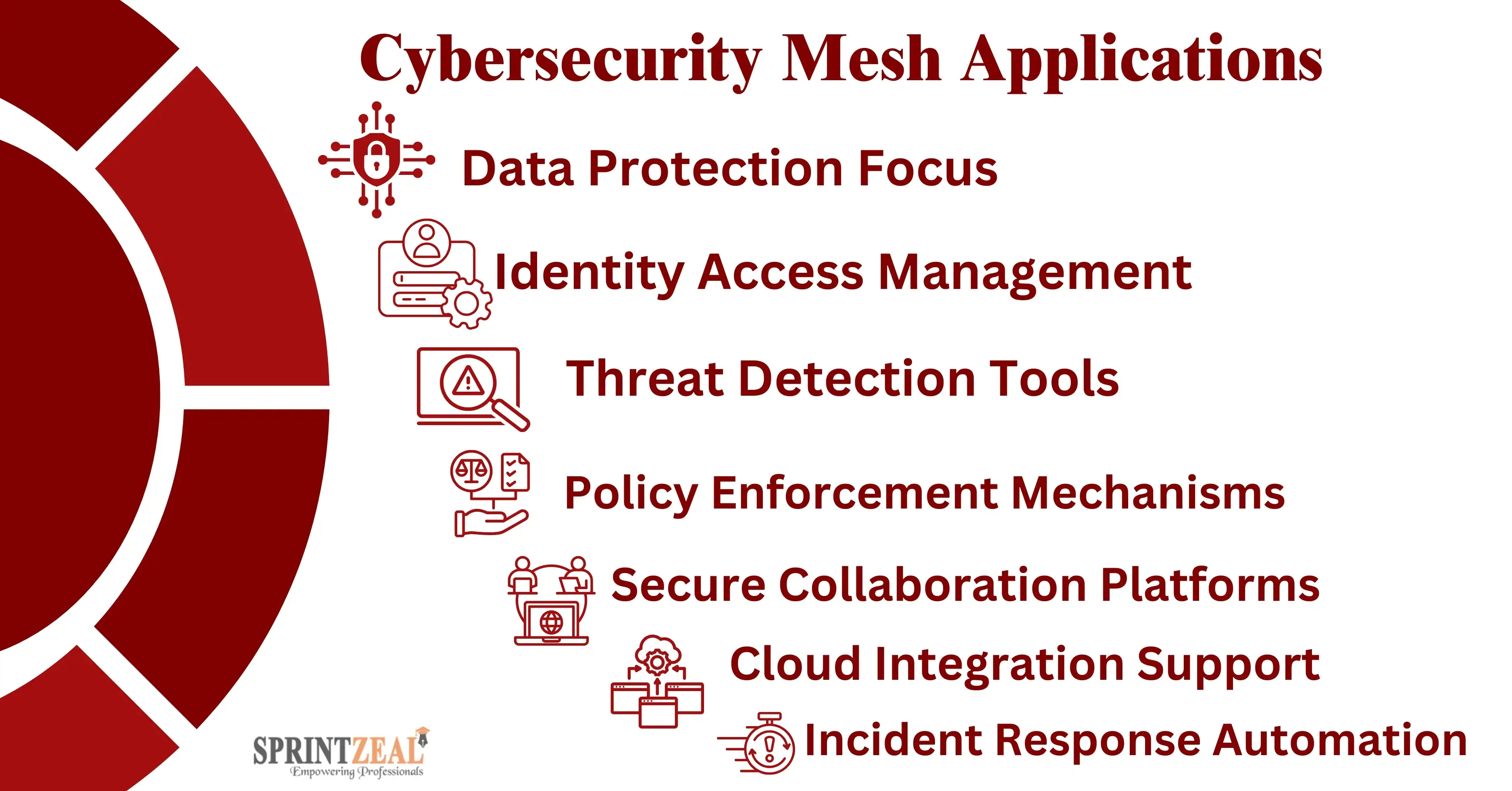
Cybersecurity mesh stands out from traditional frameworks through its innovative features, which include:
- Decentralized Security Boundaries:
Instead of relying on a single, centralized perimeter, cybersecurity mesh creates multiple micro-perimeters around digital assets, ensuring each component is independently secure.
- Seamless Integration:
It connects various security tools and technologies, allowing them to work cohesively. This integration minimizes redundancy and enhances operational efficiency.
- Dynamic Threat Intelligence:
The mesh uses AI and machine learning to adapt to different continuous learning and threats, actually providing a defensive system against newly discovered weak points.
- Granular Access Control:
This technique decreases the possibility of insider threats by ensuring that only authorized users have access to the resources available.
- Scalability and Flexibility:
Cybersecurity mesh scales effortlessly to match the organization’s growth, ensuring robust protection even as new digital assets are added.
Organizations adopting cybersecurity mesh can expect transformative benefits:
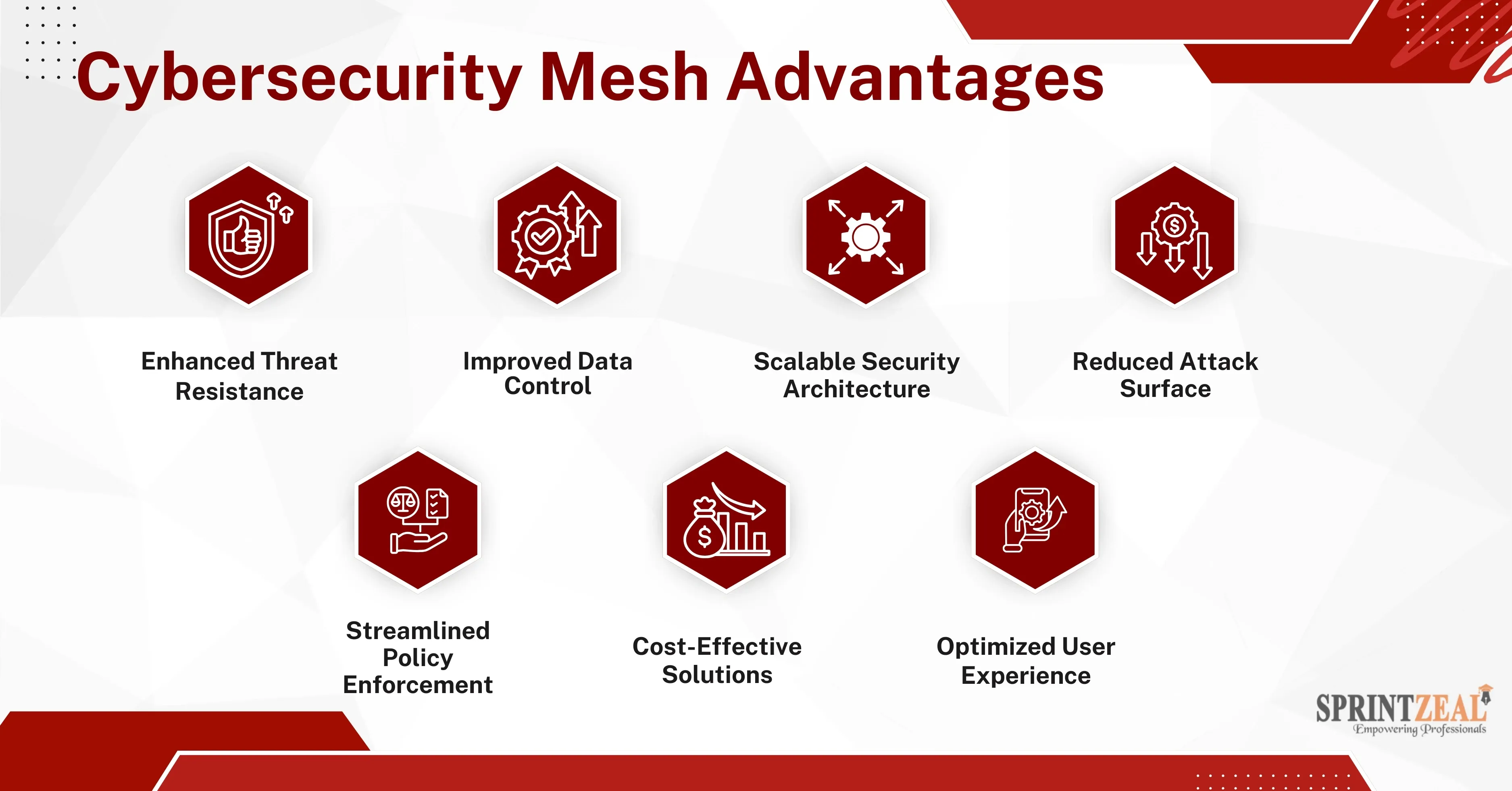
- Improved Security Posture:
By decentralizing and enhancing asset-specific security, organizations can better protect sensitive information.
- Cost efficiency:
Instead of replacing existing infrastructure, a cybersecurity mesh integrates and optimizes existing tools, reducing costs associated with complete overhauls.
- Enhanced Operational Resilience:
The number of constraints is little downtime during attacks when problems are detected and mitigated automatically.
- Regulatory Compliance:
By making it easier to comply with strict regulatory requirements, information security mesh decreases the possibility of financial penalties.
- Employee Productivity:
The architecture lessens disruptions by providing safe, role-based access, assuring that workers can perform effectively without sacrificing security.
Adopting a Cybersecurity Mesh Architecture (CSMA) offers companies an adaptable, expandable, and efficient way to address today's security issues. The four components are the policy authentication mechanism, distributed fabric, and security assessment to improve compliance, expedite, and strengthen threat intelligence.
CSMA is a great option for companies aiming to better their information security infrastructure because of the long-term advantages of extra security, effectiveness, and mitigating risk, even though the initial transition might cost money. Sprintzeal's expert-led IT Security Training Programs would then contribute to the attainment of the constant change in the cybersecurity landscape.
Obtain certifications accepted by the industry and advance your knowledge in the cutting-edge cybersecurity field. Let Sprintzeal empower you to excel—enroll today and secure your digital future!
What is cybersecurity mesh architecture?
Cybersecurity mesh architecture decentralizes security by focusing on protecting individual digital assets rather than maintaining a central perimeter. This approach enhances flexibility, scalability, and adaptability.
What is the security architecture of cybersecurity?
The organization uses structural elements and a framework known as the security architecture of cybersecurity to protect their systems and data against cyberattacks.
What are the three approaches to security in cybersecurity?
The three main approaches are:
- Prevention: Proactively identifying vulnerabilities to stop attacks before they occur.
- Detection: Monitoring systems to identify threats in real-time.
- Response: Mitigating the impact of breaches and recovering swiftly.
What is a security architect in cybersecurity?
An expert who creates, utilizes, and supervises an organization's security infrastructure is known as a security architect. They end up making certain that systems are reliable, adaptable, and in line with the corporate goals.
Thu, 18 April 2024

Tue, 16 April 2024

Wed, 26 February 2025


© 2026 Sprintzeal Americas Inc. - All Rights Reserved.
Leave a comment