Why Become a Business Analyst in 2026: Top Reasons and Scope
Thu, 18 April 2024

Follow the stories of academics and their research expeditions

IBM Data Breach – Have They Ever Been Breached?
IBM Data Breach incidents are rarely the first thing that springs to mind when one thinks of cybersecurity. This is because one of the largest tech companies in the world, IBM, has developed robust defenses against cyberattacks. Being a center of excellence, IBM is a key focus for cyberattacks because it manages enormous volumes of sensitive data and runs intricate infrastructures. Despite its extensive security measures, questions often arise: Has IBM ever suffered an IBM Data Breach? In this article, we’ll explore IBM’s approach to cybersecurity and examine how they’ve handled incidents that challenged their security systems.
International Business Machines, or IBM, has been at the forefront of technological development for over a century. IBM has an unparalleled influence on global industries due to improvements in artificial intelligence (AI), quantum computing, and enterprise software. But amazing power comes with a lot of responsibility, particularly in the field of cybersecurity. One of the leading providers of cloud and IT solutions, IBM, deals with huge quantities of sensitive data every day, making it a prime target for cyberattacks. This has sparked concerns about the potential for a company data breach, highlighting how urgently robust security measures are needed. To lower the risk of an IBM data breach, the company continues to invest heavily in modern cybersecurity technologies.
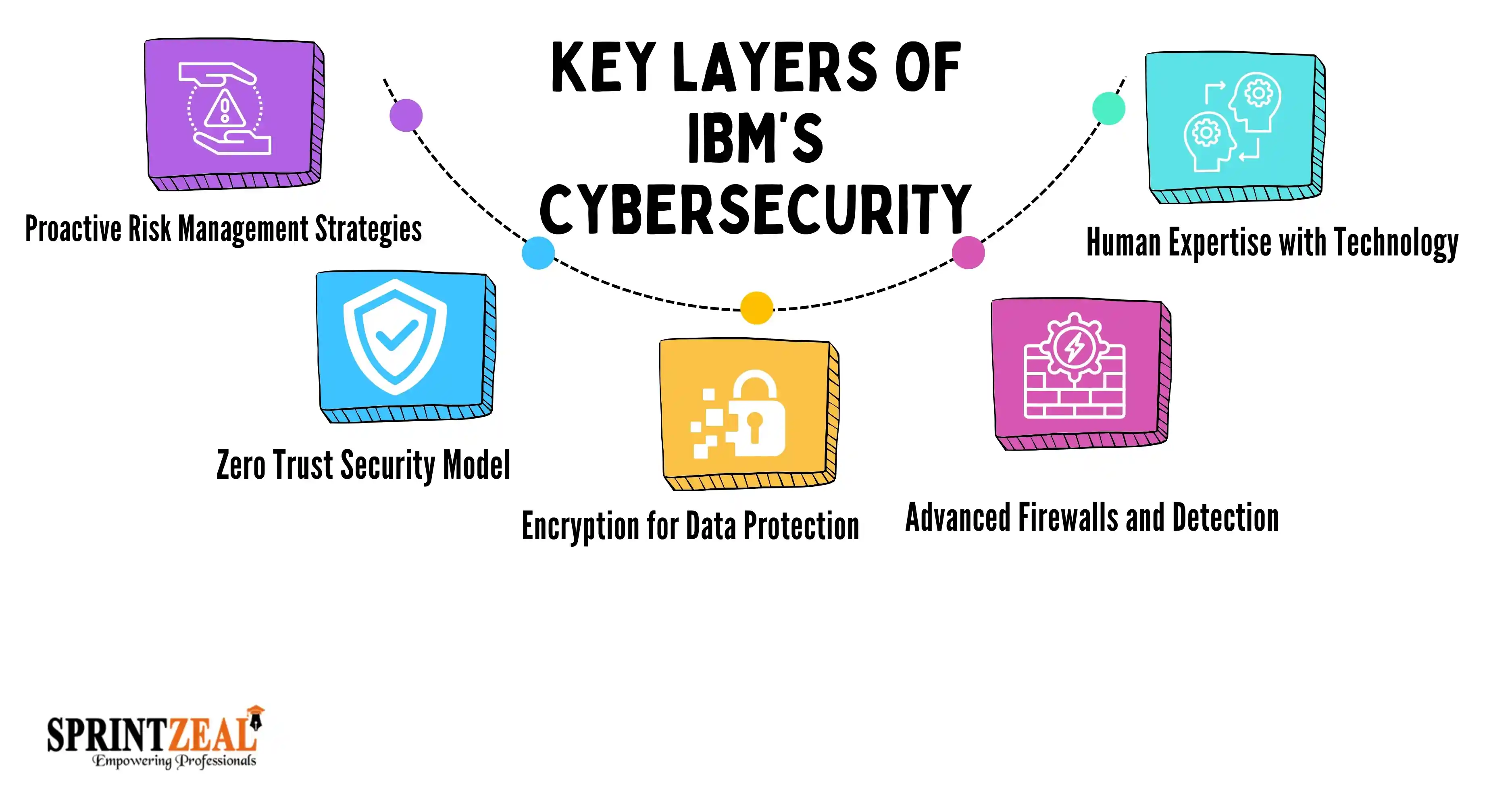
IBM’s cybersecurity success hinges on its layered approach, which includes:
The annual IBM Cost of a Data Breach report shows the financial toll that cyberattacks take. According to the 2023 report, the standard global cost of a data breach is $4.45 million. For IBM, which handles a lot of sensitive data, a breach can be very costly. The main costs include data loss from stolen information, legal costs like fines and lawyer fees, reputation damage from losing customer trust, and operational disruptions from downtime and recovery. Even with IBM's robust security measures, cyberattacks may continue for any company, so the company keeps investing heavily in cybersecurity to lower risks and potential losses.
IBM’s robust security measures have made it a leader in cybersecurity, but even giants face challenges. While no major IBM Data Breach has been officially confirmed, there have been incidents involving its services and third-party collaborations that serve as valuable lessons.
Key Incidents Highlighting IBM’s Resilience:
1) The 2019 Cloud Misconfiguration Incident:
A misconfiguration in IBM’s cloud environment briefly exposed data to potential unauthorized access.
Impact: Though not a full-blown IBM Data Breach, the incident highlighted vulnerabilities in cloud governance.
Lesson Learned: Continuous cloud security monitoring and stringent configuration audits are essential.
2) Third-Party Risks:
As IBM partners with numerous organizations, vulnerabilities in third-party systems occasionally ripple into IBM’s operations.
Example: In 2021, phishing attacks leveraged third-party email vulnerabilities, indirectly affecting IBM clients.
Lesson Learned: Third-party risk management is critical to preventing indirect breaches that could tarnish a company’s reputation.
3) Targeted Attacks on IBM Services:
IBM has been a target for cybercriminals aiming at its high-value systems.
Example: In 2020, IBM proactively identified phishing campaigns targeting its COVID-19 vaccine supply chain.
Lesson Learned: The ability to predict and respond to threats is a hallmark of advanced cybersecurity protocols.
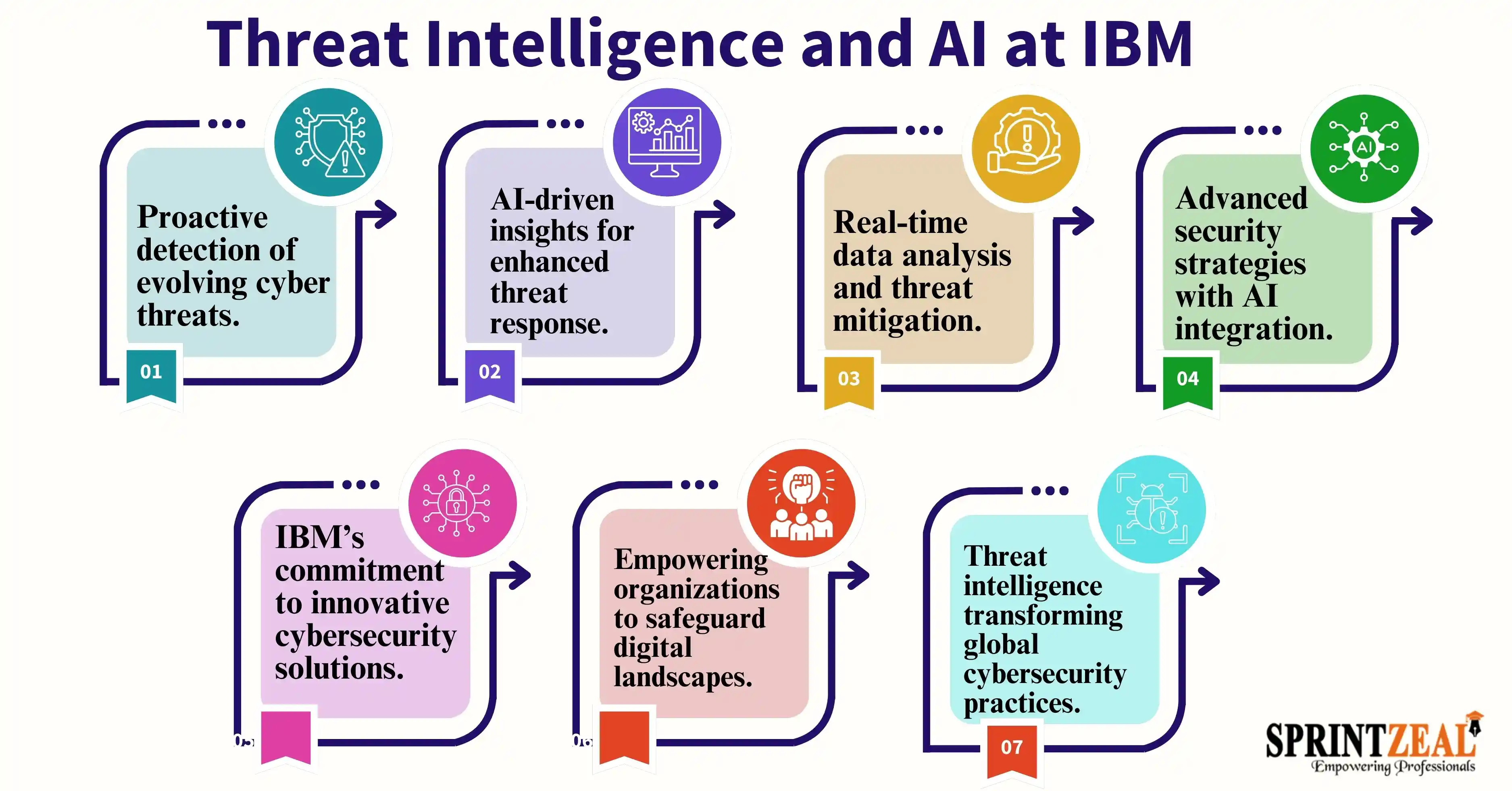
AI-driven intelligence powers the cybersecurity tools in IBM's toolbox. IBM's cognitive AI system, Watson, is vital for detecting and reducing online threats. Here's how:
For example, IBM X-Force, its cybersecurity division, uses real-time threat intelligence to combat evolving cyber risks effectively.
IBM’s success stems not just from technology but also from its deeply ingrained security-first culture:
IBM’s strategies may seem tailored for large enterprises, but businesses of all sizes can adopt these principles:
These practices can transform your organization into a cybersecurity powerhouse.
IBM’s journey in cybersecurity proves that resilience is a combination of advanced technology, proactive culture, and relentless innovation. While no organization is entirely immune to threats, IBM’s strategies highlight the importance of staying ahead of attackers. By implementing these procedures and learning new things constantly, your company can create a security framework that will last.
When you're wondering how IBM maintains its security, keep in mind that it involves more than just technology and tools; it also involves strategy, execution, and a dedication to never letting their guard down.
So, the next time you wonder how IBM stays secure, remember: it’s not just about tools and tech—it’s about strategy, execution, and a commitment to never letting their guard down. Subscribe to all our course pages and gain unlimited access to IT and cybersecurity training. Take classes like CompTIA Security+, CISSP, CISA and others to learn from professionals. Regardless of your career stage, Sprintzeal assists you in reaching your objectives.
Thu, 18 April 2024

Tue, 16 April 2024

Wed, 26 February 2025


© 2026 Sprintzeal Americas Inc. - All Rights Reserved.
Leave a comment