Information Assurance Model in Cybersecurity
-
 By Niharika Chaurasia
By Niharika Chaurasia - Published on Jun 6 2023

Table of Contents
Introduction
Welcome to the digital age, where protecting personal data privacy of personal data is crucial. Strong information assurance practices must be implemented by organisations due to the increase in cyber threats.
Discover about the information assurance model and how it contributes to the protection of our digital assets in this article. Investigating its importance in the realm of cybersecurity and how it forms the basis for protecting sensitive data would be beneficial.
So grab a cup of coffee and learn the secrets of information assurance model and its importance in today's linked world.
Understanding the Information Assurance Model
Information assurance encompasses the policies, processes, and technologies employed to protect and manage information assets. The Information Assurance Model provides a structured approach to achieving this goal.
It consists of four key components:

Confidentiality
Safeguarding data from unauthorized access ensures that only authorized individuals can access and view sensitive information. Encryption, access controls, and secure communication protocols play a pivotal role in maintaining confidentiality.
Example: An organization implements strong encryption protocols to protect customer data during transmission. To keep your data locked away from prying eyes, organizations employ advanced encryption algorithms like AES (Advanced Encryption Standard) or RSA (Rivest-Shamir-Adleman).
These algorithms act like digital bodyguards, ensuring that even if someone manages to intercept your data, it's like reading a jumble of secret code.
Integrity
Maintaining data integrity ensures that information remains accurate, complete, and unaltered throughout its lifecycle. Techniques such as data validation, checksums, and digital signatures are employed to detect and prevent unauthorized modifications.
Example: A financial institution employs data validation techniques in its banking systems.
When you make a transaction, the system is there to safeguard your data's integrity. It carefully checks if everything matches the rules and criteria in place.
If anything seems off, like an incorrect account number or an unusually large transaction amount, the system steps in as a protector and blocks the transaction. This ensures that your data remains accurate and shielded, preserving the trustworthiness of your information.
Availability
To ensure information availability, resilient systems and processes are crucial. This information assurance model component checks on backup and disaster recovery strategies, redundancy measures, and proactive monitoring.
Example: an e-commerce website ensures uninterrupted service by employing multiple synchronized servers and a load balancer. This smart setup evenly distributes incoming requests, preventing disruptions caused by server failures or sudden traffic surges.
As a result, customers can seamlessly browse, shop, and complete transactions, even during peak times or when a server encounters issues.
Non-Repudiation
Non-repudiation ensures that the origin and integrity of data cannot be denied by the sender. Digital signatures, audit trails, and timestamping mechanisms are utilized to provide evidence of the authenticity and integrity of digital transactions.
Example: An organization implements a digital signature mechanism in its document management system. A distinct cryptographic signature is generated and added to the document when it is digitally signed by an authorised user. This signature prevents the signer from later disputing their involvement in the document by providing proof of the document's integrity, legitimacy, and identity.
Statistics on Cyber Threats and Need for Information Assurance
To comprehend the urgency and relevance of information assurance, let's consider some eye-opening statistics:
-According to a report by Risk Based Security, in 2021 alone, there were over 5,258 reported data breaches, exposing more than 1 billion records.
-The Ponemon Institute's Cost of Cyber Crime report revealed that the average cost of a data breach in 2021 was a staggering $4.24 million.
-A study by Verizon showed that 85% of successful data breaches involved some form of human interaction, such as social engineering or phishing attacks.
These statistics underscore the pressing need for organizations to implement robust information assurance measures to mitigate the risk of cyber threats.
Best practices of Information Assurance Model
Let's dive into some real-world examples and best practices that showcase how organizations implement the Information Assurance Model:
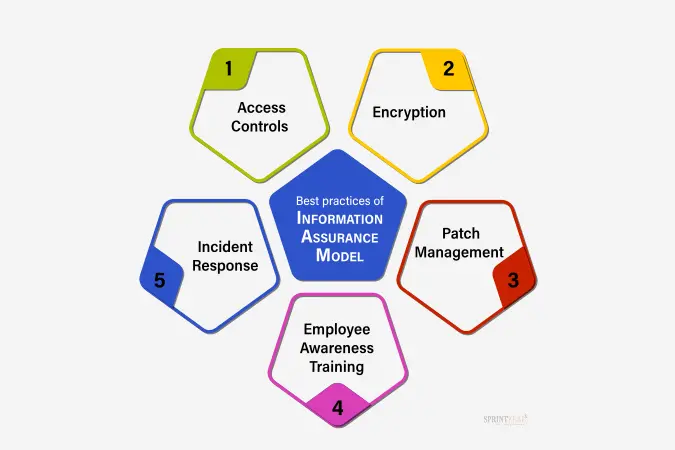
Access Controls
Organizations put measures in place to control who can access sensitive data. It involves the use of secure passwords, two-factor authentication (such as inputting a number delivered to your phone), and role-based access control (which grants access depending on employment duties).
By doing this, they offer an additional degree of protection by making sure that only authorised individuals may access the data.
Encryption
Encryption transforms sensitive information into a secret code, ensuring its protection. To prevent unauthorized access and secure communication, techniques like Transport Layer Security (TLS) are employed. Even if someone intercepts the data, they cannot decipher its meaning without the decryption key.
Patch Management
Keeping software up to date is crucial for cybersecurity. Regularly applying security patches and updates to operating systems, applications, and network devices helps address known vulnerabilities. By doing this, organizations minimize the risk of exploitation by hackers who might try to exploit those vulnerabilities.
Employee Awareness Training
Organizations invest in training their employees to be cybersecurity savvy. This includes teaching them how to identify phishing attempts (fake emails that try to trick you into sharing sensitive information), practicing good password hygiene (like using strong passwords and not sharing them), and reporting any suspicious activities they come across.
By making employees aware of these best practices of information assurance model, organizations strengthen their defense against cyber-attacks.
Incident Response
During a security breach, an effective incident response plan is vital. It minimizes damage, investigates the breach, and restores normal operations swiftly. This plan ensures prompt action and prevents further harm.
By implementing the Information Assurance Model, organizations protect their data and systems. These examples and best practices of information assurance model establish a strong security framework, defending against cyber threats and keeping sensitive information safe.
Certification Courses Related to Information Assurance Model
Strengthen your existing cybersecurity expertise, by pursuing certification courses related to the Information Assurance Model can open doors to exciting opportunities.
Certified Information Systems Security Professional (CISSP)
A highly recognized certification offered by (ISC)², focusing on various domains of information security, including governance, risk management, cryptography, and security operations.
Certified Information Security Manager (CISM)
This certification is designed for professionals responsible for managing an enterprise's information security program. It covers topics such as information security governance, risk management, incident management, and program development.
Certified Information Systems Auditor (CISA)
CISA is ideal for professionals involved in auditing, control, and security of information systems. It emphasizes topics such as information system governance, risk management, and acquisition, development, and implementation of information systems.
CompTIA Security+
It is a foundational certification that imparts a thorough knowledge of cybersecurity ideas and best practises. It includes subjects including incident response, risk management, and network security.
GIAC Security Essentials (GSEC)
This certification validates an individual's understanding of information security concepts and technologies. It covers areas such as access controls, network security, and cryptography.
Certified Information Privacy Professional (CIPP)
This certification focuses on privacy regulations and best practices. It equips professionals with knowledge about privacy laws, data protection strategies, and privacy program management.
EC-Council Certified Ethical Hacker (CEH)
This certification trains professionals to think like hackers and identify vulnerabilities in systems. It covers topics such as network scanning, system hacking, and ethical hacking methodologies.
ISACA Certified in the Governance of Enterprise IT (CGEIT)
CGEIT is designed for professionals responsible for governance and strategic management of IT resources. It emphasizes areas like IT governance frameworks, strategic alignment, and risk management.
Offensive Security Certified Professional (OSCP)
This certification focuses on practical skills in penetration testing and ethical hacking. It requires hands-on experience and assesses the ability to identify and exploit vulnerabilities in systems.
ISACA Certified Information Systems Auditor (CISA)
CISA focuses on auditing, control, and security of information systems. These certification courses delve into essential topics like information system governance, risk management, and information systems development. They equip professionals with the necessary expertise to thrive in the ever-changing realm of information assurance.
By earning these certifications, individuals showcase their proficiency in safeguarding information assets, managing risks, and implementing robust cybersecurity measures.
Master Cybersecurity with Sprintzeal's Courses
Are you looking to upskill your cybersecurity career? Look no further than Sprintzeal's comprehensive cybersecurity courses. These courses are the ideal method to keep ahead in this quickly expanding industry because they are made to provide professionals with the most recent knowledge and abilities.
You can select the course that best suits your professional objectives from options like Certified Information Systems Security Professional (CISSP), Certified Information Security Manager (CISM), and CCSP Certification Training Course (CCSP). Whether you're interested in information security governance, risk management, or ethical hacking, Sprintzeal has got you covered.
Don't miss out on the opportunity to boost your professional credentials and stand out in the competitive cybersecurity landscape.
Conclusion
In today's digital landscape, information assurance is crucial for ensuring the security and accessibility of sensitive data. By embracing the Information Assurance Model, organizations can proactively protect themselves against emerging cyber threats.
It's essential for stakeholders to understand the importance of information assurance and allocate resources to strengthen their cybersecurity defenses. This builds trust among customers, partners, and stakeholders while mitigating the devastating consequences of data breaches.
Are you ready to level up your skills? Explore Sprintzeal's cybersecurity courses and unlock your potential today! Contact us now to embark on your journey to success.
Subscribe to our Newsletters
Popular Programs
CISSP® - Certified Information System Security Professional
Live Virtual Training
- 4 (964 + Ratings)
- 38k + Learners
CISA® - Certified Information System Auditor
Live Virtual Training
- 4.4 (426 + Ratings)
- 34k + Learners
CISM® - Certified Information Security Manager
Live Virtual Training
- 4 (200 + Ratings)
- 30k + Learners
CCSP® - Certified Cloud Security Professional
Live Virtual Training
- 5 (964 + Ratings)
- 61k + Learners
Trending Posts
Cybersecurity Fundamentals Explained
Last updated on Feb 2 2024
What is Data Security - Types, Strategy, Compliance and Regulations
Last updated on May 26 2023
CISM certification cost details
Last updated on Jul 15 2022
Why and How to Perform a Risk-Based Internal Audit
Last updated on Jan 9 2024
Risk-based Audit Planning Guide for Beginners
Last updated on Dec 6 2023
Understanding Risk assessment in audit planning
Last updated on Dec 4 2023
Categories
- Agile Management 55
- AI and Machine Learning 44
- Big Data 53
- Business Management 52
- Cloud Computing 44
- Digital Marketing 56
- Information Security 8
- IT Hardware and Networking 17
- IT Security 103
- IT Service Management 29
- Leadership and Management 1
- Microsoft Program 2
- Other 45
- Programming Language 31
- Project Management 162
- Quality Management 75
- Risk Management 8
- Workplace Skill Building 2
Trending Now
Which Certification is best for Cybersecurity?
ebookTop 5 Compelling Reasons To Get A Cyber Security Certification
ebookHow to Become IT Security Expert with CISSP Certification
ebookTop 20 Reasons You Should Get a CISSP Certification
ebookCISM certification cost and career benefits
ebookWhat is CISSP? – Everything about CISSP Certification Explained
ebookPass CISSP Exam - How to Clear CISSP Exam in First Attempt 2024 (UPDATED)
ebookCISSP Certification – Top 25 Career Benefits in 2024
ebookCybersecurity – Everything You Need to Know About it
ebookCybersecurity Strategy: Building a Strong Defense for Business
ebookCyber Attack Statistics and Trends to Know in 2024
ebookUpdated Google Certification Training Course list 2024
ArticleWhich Cybersecurity Certification Should I Get First?
ebookCysa+ certification – Should you get it?
ebookList of Top Security Certifications
ArticleEasiest Security Certification to Get
ebookCybersecurity Fundamentals Explained
ebookISACA Certifications List 2024
ebookCareer Benefits of CISM Certification in 2024
ArticleList of Top Information Security Certifications in 2024
ebookCISM certification cost details
ArticleSafeguarding Digital Domain: 10 Most Common Cybercrimes
ebookMitigate the Cyber-Attack Risks with Best Cyber Security Protocols
ebookCybersecurity Interview Questions and Answers 2024
ebookData Leak - What is it, Prevention and Solutions
ebookTop Cybersecurity Software Tools In 2024
ebookWhat is Cryptography - A Comprehensive Guide
ebookInformation Security Analyst - Career, Job Role, and Top Certifications
ebookCyber Security Analyst - How to Become, Job Demand and Top Certifications
ebookIBM Data Breach: Is IBM Really Breach-Proof?
ArticleWhat is the Department of Defense (DoD) Directive 8140
ebookWhat is Data Security - Types, Strategy, Compliance and Regulations
ebookData loss Prevention in Cyber Security Explained
ebookCybersecurity Controls Explained in Detail
ebookCybersecurity Framework - A Complete Guide
ebookCybersecurity Career Paths Guide
ebookFuture of Cybersecurity - Trends and Scope
ebookScope for Cybersecurity in 2024 - Update for 2024
ebookCyber Security Careers and Outlook - 2024 Guide
ebook5 Cybersecurity Predictions in 2024 - Trends and Challenges
ebookEthical Hacking Career: A Career Guide for Ethical Hacker
ebookApplication Security: All You Need To Know
ebookCybersecurity Roles - Top Roles and Skills to Consider in 2024
ebookHow to Get Cyber Essentials Certified
ebookTop 10 Cyber Security Threats and How to Prevent Them
ebookTop 10 Network Scanning Tools of 2025
ebookCyber Incident Response Plan: A Comprehensive Guide
ebookInformation Assurance Careers - Exploring Career Paths
ebookCybersecurity Mesh Architecture: What It Is and How to Build It
ebookWhat is Threat Modeling? Methodologies, Types, and Steps
ebookWhat is Digital Forensics? Types, Process & Challenges
ebookRecent Cyber Attacks & Data Breaches in 2024
ebookHow to Become an Information Security Analyst Salary, Skills, and More
ArticleList of Top Department of Defense (DoD) Approved 8570 Certification Courses
ebookTop 5 Ransomware Attacks to Watch Out for in 2024
ebookJob Prospects for DoD Certified Professionals: A Pathway to Success in cybersecurity
ebook10 Biggest Data Breaches of the 21st Century
ebookWhat is a Cybersecurity Incident?-Types, Impact, Response Process and More
ebookCyber Security Planning - A Detailed Guide for Risk Mitigation
ebookWhat is Cybercrime? Exploring Types, Examples, and Prevention
ebookCybercrime Impacts On Business: 6 Major Effects
ebook5 Types of Cyber Attacks You Should Be Aware of in 2024
ebookCloud Cyber Attacks: Causes, Types, Prevention and Protection
ebookCloud Malware: Types of Attacks and Security Measure
ebookList Of Top Cybersecurity Threats In 2024
ebookRisk-based Audit Planning Guide for Beginners
ebookDemystifying Cloud-Based Cyber Attacks: A Comprehensive Guide
ebookPrevent Cyber Attacks: Strategies to Protect Your Digital Assets
ebookList of Top 10 Cybersecurity Careers in 2024
ebookTop 20 Cybersecurity Trends to Watch Out for in 2024
ArticleHow to Become Cybersecurity Engineer
ArticleUnderstanding Risk assessment in audit planning
ArticleFundamentals of Risk-Based Auditing: A Strategic Framework
ArticleTop 8 Types of Cybersecurity Jobs and Salary Insights
ArticleA Comprehensive Guide to Building Risk-Based Internal Audit Plan
ArticleRisk-Based Internal Auditing Approaches: 7 Steps to Explore
ArticleCompTIA Security+ 601 vs. 701: Understanding Key Differences
ArticleWhy and How to Perform a Risk-Based Internal Audit
ArticleRisk-Based Auditing Techniques Explained
ebookEthical Hacking Tools: Best Ones for Cybersecurity in 2025
ArticleEvolving Cyber Threats and Vulnerabilities in Cybersecurity Risk Management
ArticleWhat Is Secure Access Service Edge (SASE)?
ArticleHow to Stay Cyber-Secure in Work and Personal Life (Tips and Practices)
ArticleTarget Cyber Attack: Key Lessons from the 2013 Data Breach
ArticleLinkedIn User Data Protection Explained
ArticleCanva Data Breach: Best Lessons for Users and Businesses
ArticleHow Did Capital One Respond to Their Major Cyber Incident?
ArticleWhat Innovative Measures Did Reddit Take to Protect User Data?
ArticleHow Does Slack Respond to Security Challenges?
ArticleTwitch Data Breach: Response, Changes, and Key Takeaways
ArticleGuess What Google Did When a Employee Breached Their Firmware
ArticleWhat Happened When Cisco Faced a Cyber Incident?
ArticleWhat Sony Did to Rebuild Trust After a Major Cyberattack
ArticleHow to Handle a Data Breach? Learn from Microsoft!
ArticleCybersecurity Mesh: A New Approach for Security Design
ArticleHow Target Turned a Cyber Crisis into a Lesson for All
ArticleDropbox Data Breach: What Companies Can Learn from It
ArticleHow JPMorgan Chase Strengthened Security After Facing Cyber Threats
ArticleThe Future of Online Security: Trends to Watch in 2025
ArticleLatest Trends in CyberSecurity
ArticleTop 12 Cyber Security Apprenticeships with High Earning Potential in 2025
ArticleEnhancing Safety and Competence in Today's Workplace
Article
















