Why Become a Business Analyst in 2026: Top Reasons and Scope
Thu, 18 April 2024

Follow the stories of academics and their research expeditions

In the world of the financial sector, data is the new currency, and securing it from cybercriminals is vital. With every advancement and online transaction in digital banking, there is an increase in cybercriminals creating better approaches to exploit vulnerabilities. A notable example is the 2014 cyber attack on JPMorgan Chase, which resulted in a data breach of over 83 million customers and businesses.
But how did they do it? Let’s explore the story behind JPMorgan Chase’s transformation in Cyber security and network security.
Before that Learn more about how cybersecurity is reshaping the financial industry in our blog.
The 2014 data breach at JPMorgan Chase was one of the greatest in history. This breach was a wake-up call for one of the world's most prominent banks, revealing inadequacies inside the cybersecurity system and starting a sacrificial table of the attack. JPMorgan Chase turned this emergency into an opportunity, leveraging advances to organize security arrangements, solid preparation programs, and cutting-edge innovations to regain its position as a pioneer in cybersecurity quality.
"Explore other notable cybersecurity incidents in our article Top 10 Cybersecurity Breaches in the 21st Century and What We Can Learn.
This attack shocked the financial world and raised several critical questions, like how could one of the top banks in the USA fall prey to cybercriminals? What steps can be taken to overcome such types of incidents in the future?Here let's go.
In spite of the fact that there's no money-related misfortune due to an information breach, the harm to JPMorgan Chase's notoriety was evident. Clients stressed approximately their individual information, and the bank confronted an expanded examination from controllers.
JPMorgan Chase allocated billions of dollars to fix the data breach and also regained customer trust and upgraded its cybersecurity measures.
The breach taught three essential lessons:
After confronting the greatest information breach, JPMorgan Chase adopted a multi-layered cybersecurity strategy to ensure such episodes would not happen again.
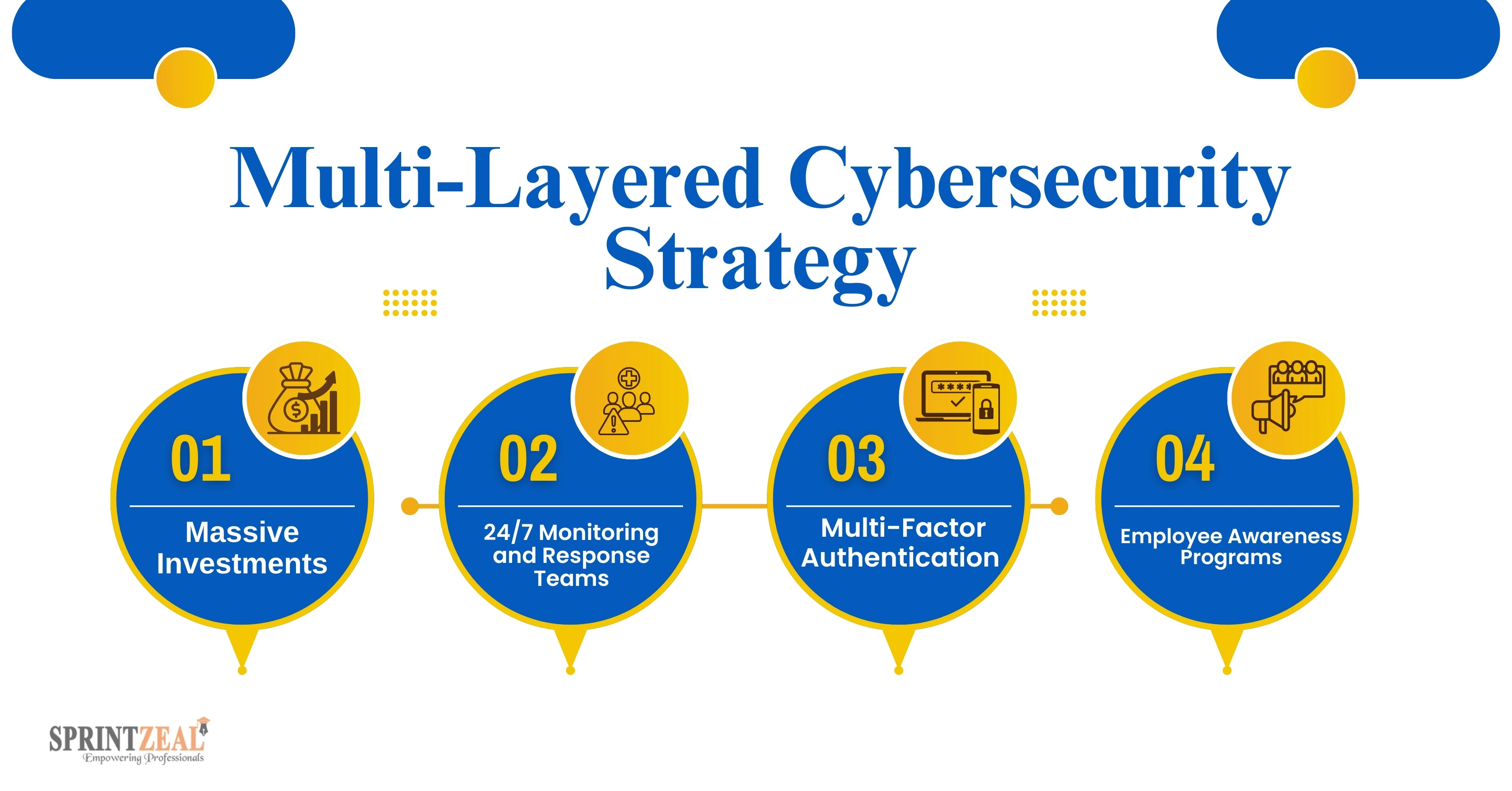
The bank contributed over $500 million each year in cybersecurity, making it one of the most noteworthy contributions within the monetary division. This fund was utilized to overtake systems, enlist top-tier cybersecurity ability, and actualize unused advances.
A dedicated team of experts was established to monitor network activity around the clock. They focused on detecting cyber attacks in real-time and minimizing potential damage.
To secure client accounts, JPMorgan Chase executed MFA; this will maintain a strategic distance from unauthorized access to cyber assailants indeed in the event that login qualifications were stolen.
Broad preparation programs are executed to teach workers approximately phishing tricks, information security conventions, and the best homes for secure online behavior.
JPMorgan Chase grasped inventive innovations to boost its guards against information breaches and other cyber dangers. You can explore this detailed guide on cyber threats in cybersecurity risk management.

AI and ML are at the cutting edge of the bank's cybersecurity methodology. These advances analyze endless sums of information, distinguish designs, and anticipate potential vulnerabilities.
The bank adopted network segmentation to limit the movement of attackers within its systems. Even if a breach occurred, segmented networks ensured that damage was contained.
To defend touchy client information, JPMorgan Chase updated its encryption conventions, guaranteeing that indeed, in the event that information was caught, it would stay garbled to unauthorized parties.
JPMorgan Chase tied up with driving cybersecurity firms to remain ahead of rising dangers. These collaborations given the bank will get to the most recent instruments and risk insights.
JPMorgan Chase has not, as it modified its cybersecurity system but has moreover gotten to be a pioneer within the field. It proceeds to create advanced advances like quantum computing and blockchain to update security updates.
1. Industry Authority
By sharing its learnings and techniques, JPMorgan Chase is making a difference and setting industry-wide standards for cybersecurity within the money-related segment.
2. Commitment to Development
The bank frequently overhauls its frameworks, arrangements, and conventions to adjust to the ever-changing scene of cyber dangers.
It isn’t a surprise that all these factors saw a direct impact on the ability of JPMorgan Chase to prevent the cyber breach. These events may prove to be extremely detrimental to the company’s operating capabilities, giving them a reason to do everything possible to invest in their security frameworks.
As a company that is reportedly one of the world’s largest, the chances of a cyberattack on such a company will always remain high; however, such events will no longer remain a surprise given the company’s extensive security enhancements post the aforementioned breaches.
To master threat detection and build a comprehensive risk detection framework, consider enrolling in a reputable certification training provider like Sprintzeal.Our top certifications, Cybersecurity Fundamentals Specialist, CISSP® - Certified Information System Security Professional, and Cybersecurity Risk Assessment Specialist, provide you with an in-depth understanding of the latest industry materials.
Thu, 18 April 2024

Tue, 16 April 2024

Wed, 26 February 2025


© 2026 Sprintzeal Americas Inc. - All Rights Reserved.
Leave a comment