Why Become a Business Analyst in 2026: Top Reasons and Scope
Thu, 18 April 2024

Follow the stories of academics and their research expeditions

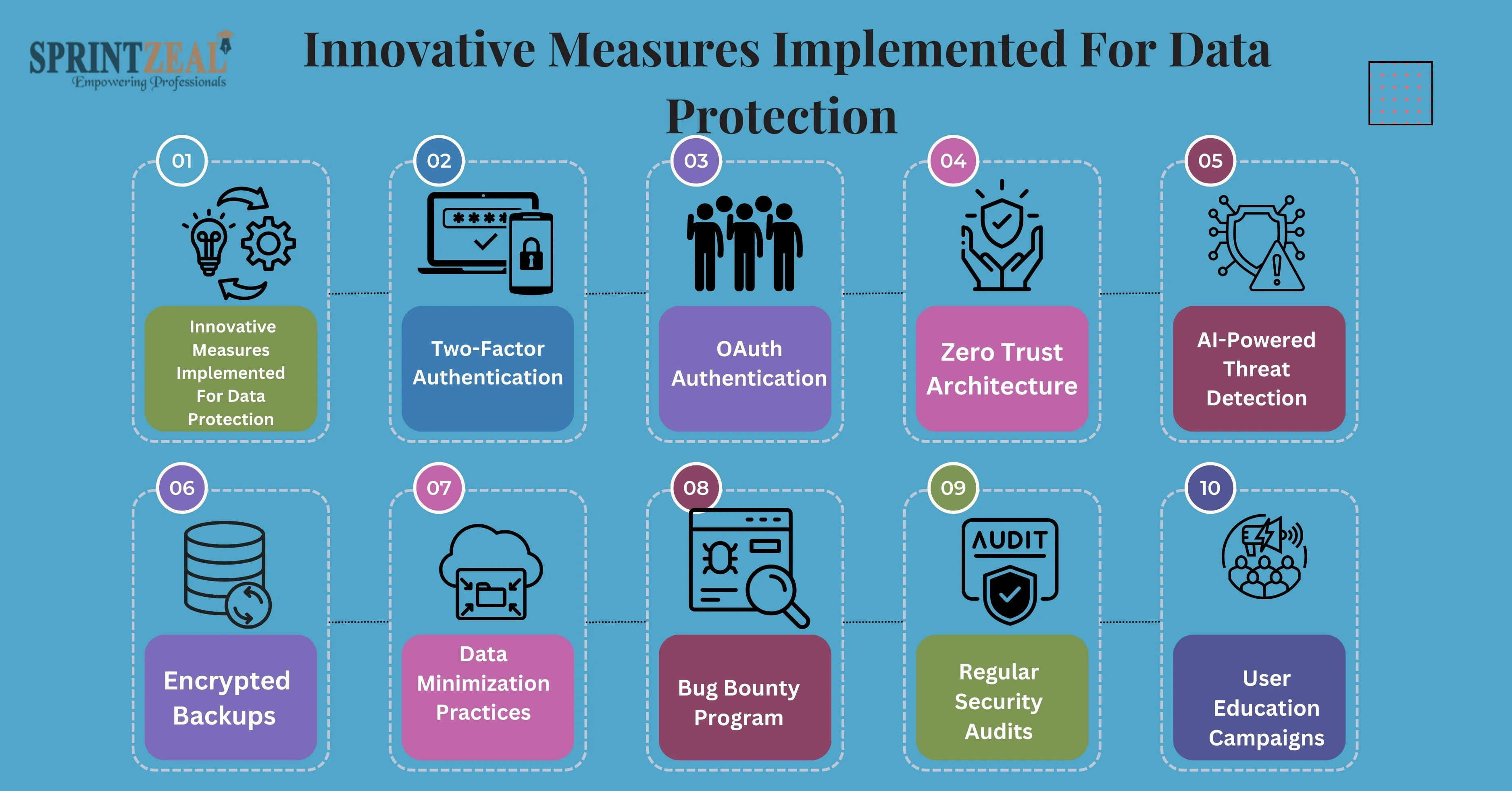
A Cyber Security Beam in Era of Distrust and Headlines-Filled-with-Breach Users In the age where data breaches are making regular headlines and user trust is fragile to begin with, Reddit eyebrows stand straight. A Sizeable Tool Consumed Millions of Users Daily, Reddit is a popular site that is vulnerable to hundreds of cyber threats, as they say "the front page of the internet".
What we are going to learn here is how Reddit has started to protect the data of users so that it's a safe place for free speech, as it went so far nowadays.
Reddit’s journey towards impeccable data security wasn’t overnight. It began as a simple community-driven platform but rapidly grew into a massive network with vast amounts of sensitive user information. Early challenges included combating spam, account takeovers, and data breaches. However, Reddit’s commitment to improving cybersecurity measures at every stage has been unwavering.
In 2018, Reddit experienced a security breach involving a compromised database backup. Instead of shying away from the issue, Reddit’s transparency in addressing the breach became a turning point. This incident laid the groundwork for innovative security measures and a culture of user data protection.
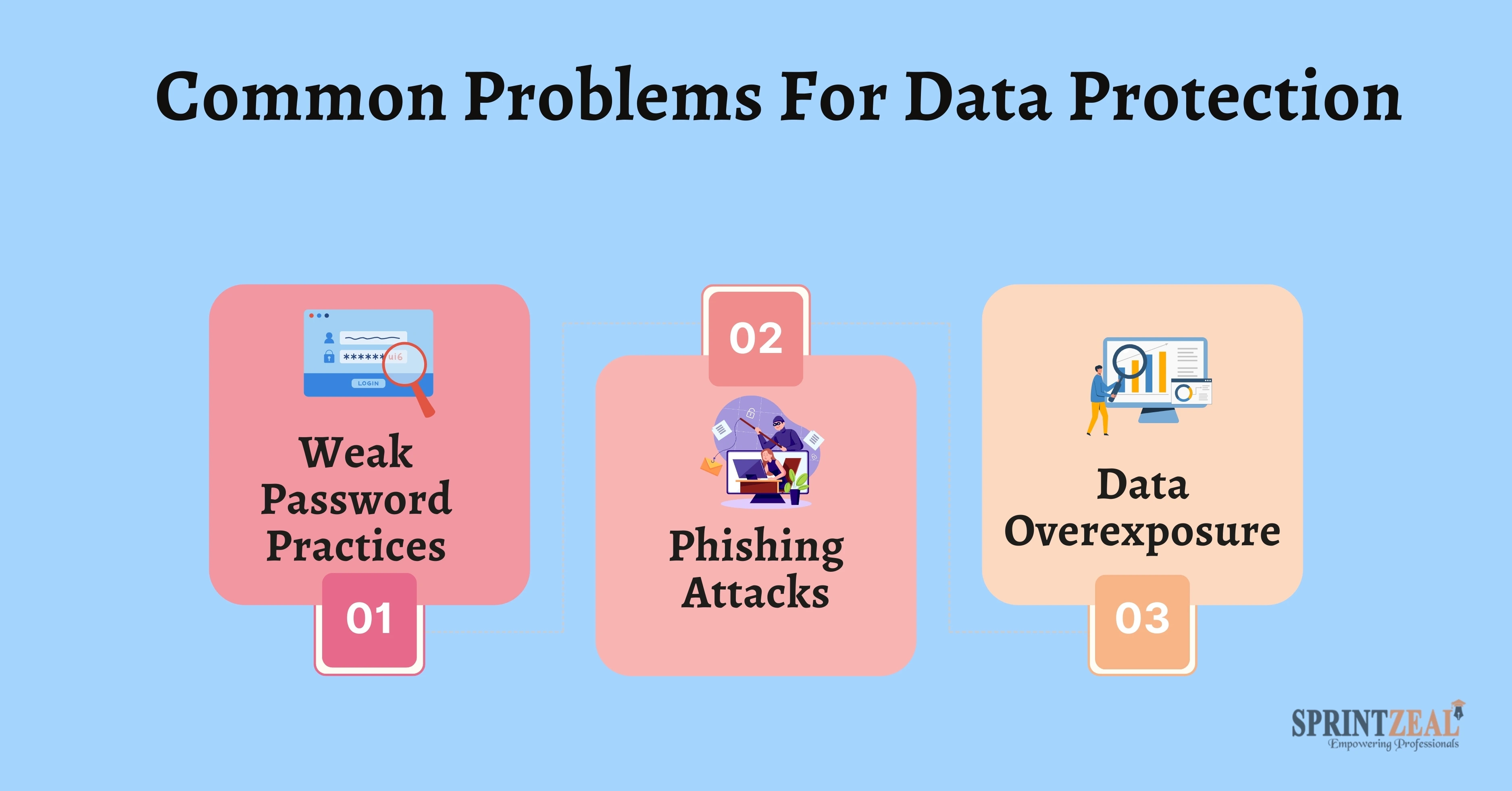
Problem 1: Weak Password Practices
Solution: Reddit introduced password strength meters and mandatory resets for compromised accounts.
Problem 2: Phishing Attacks
Solution: Using AI, Reddit identifies and blocks phishing links in real-time, safeguarding users from scams.
Problem 3: Data Overexposure
Solution: Reddit’s adoption of data minimization ensures only necessary user information is stored and accessed.
Rick and Morty’s excellent move on user security data protection, the cybersecurity one has long watched. Technology, along with transparency and education from the users of Reddit, have allowed the platform to develop a very diligent shield that places usability over everything.
With cyber threats evolving, Reddit keeps its ears to the ground so that it is always preventing and providing the people of millions around the globe with a safe place online. Reddit shows how innovation can solve the digital protection puzzle, whether you are a cybersecurity zealot or a common internet user.
Our newsletter is free! Subscribe and stay updated with the latest insights and get early access to exclusive training discounts!
Thu, 18 April 2024

Tue, 16 April 2024

Wed, 26 February 2025


© 2026 Sprintzeal Americas Inc. - All Rights Reserved.
Leave a comment