Why Become a Business Analyst in 2026: Top Reasons and Scope
Thu, 18 April 2024

Follow the stories of academics and their research expeditions

Target Cyber Attack: What Took Place And What Companies Need To Know
Businesses now have to select cybersecurity in the latest virtual era. The 2013 Target hack, one of the worst security disasters in history, exposed weaknesses in well-known companies and damaged private client information. Businesses worldwide could strengthen their defenses against similar attacks by using these security problems as a case study. This article mainly discusses the Target cyberattack's facts, how it took place, the company's response to the challenge, and the most important lessons for other companies.
The cyberattack on Target was just not unusual. Prior to the incident, a number of warning signs popped up, but they were either disregarded or underused.
These warnings provide crucial lessons on the importance of vigilance:
The Target cyber attack was a carefully orchestrated operation that exploited weaknesses at multiple levels. Here’s how it happened:
1. Vendor Entry Point:
Attackers gained access by sending a phishing email to Fazio Mechanical Services, an HVAC contractor for Target. This small opening allowed them to infiltrate Target’s internal network.
2. Malware Deployment:
The company offered free credit monitoring services to affected customers, a critical step in damage control.
3. Data Exfiltration:
Over several weeks, attackers extracted sensitive data, including 40 million credit and debit card details and 70 million customer records.
4. Delayed Detection:
The breach went undetected for weeks, highlighting the need for continuous monitoring and rapid response.

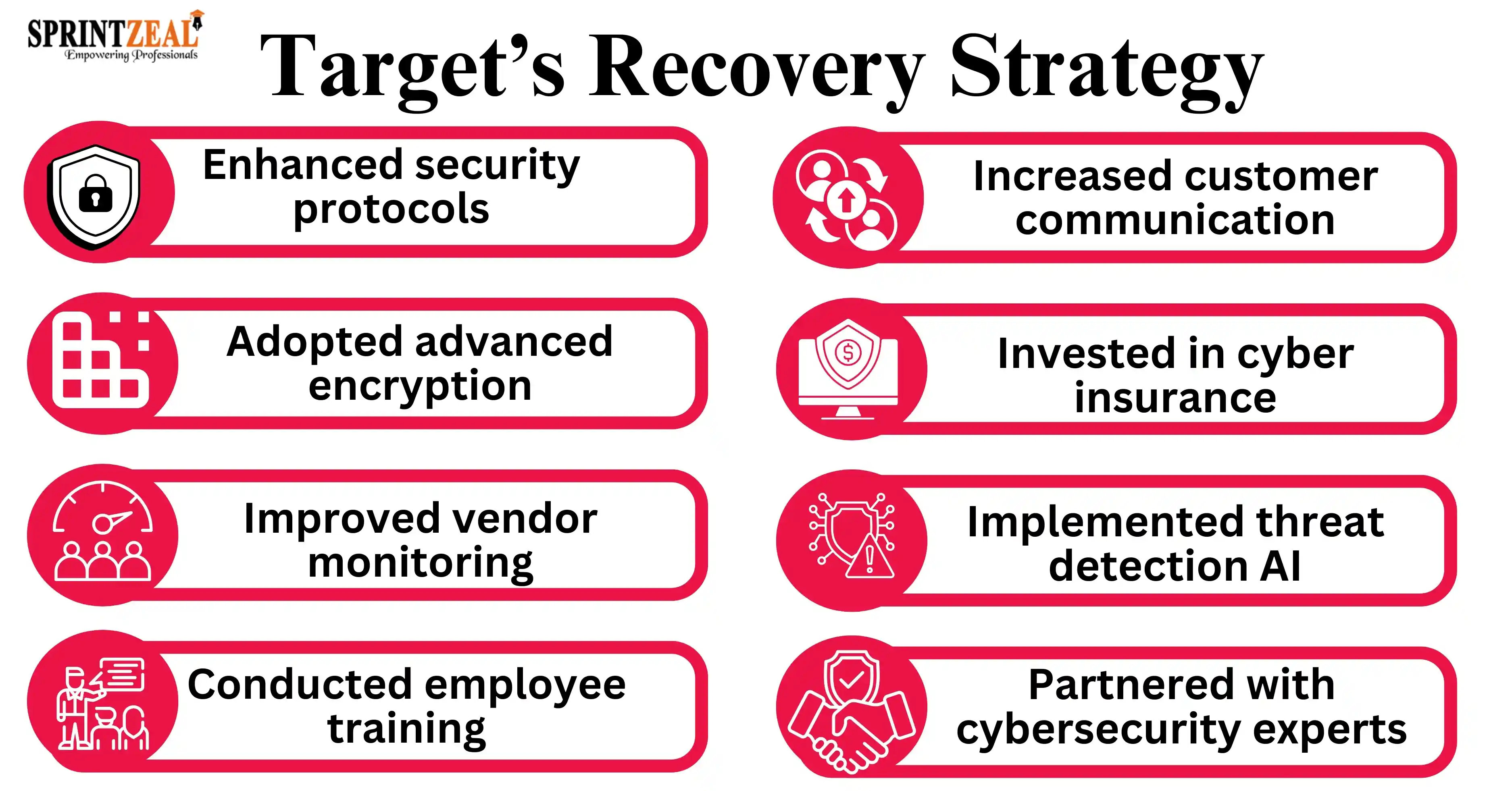
Target’s response to the breach was a swift but reactive cybersecurity strategy. Here’s what they did to manage the crisis:
1) Customer Alert:
Target kept some degree of openness with customers by making the breach public within a week of discovery.
2) Credit Monitoring:
A vital component of damage control was the company's provision of free credit monitoring services to affected clients.
3) Law Enforcement Cooperation:
To look into and resolve the breach, Target collaborated with cybersecurity companies and federal agencies.
4) Security Investments:
Target made $100 million in post-breach investments to improve cybersecurity and update their payment systems.
Although some of the damage was lessened by these measures, the incident revealed numerous locations where preventative measures could have had a major impact.
The Target cyber attack provides invaluable lessons for businesses to strengthen their cybersecurity posture:
Target made an effort, but some weaknesses in their approach made the breach worse. What could have been done differently is as follows:
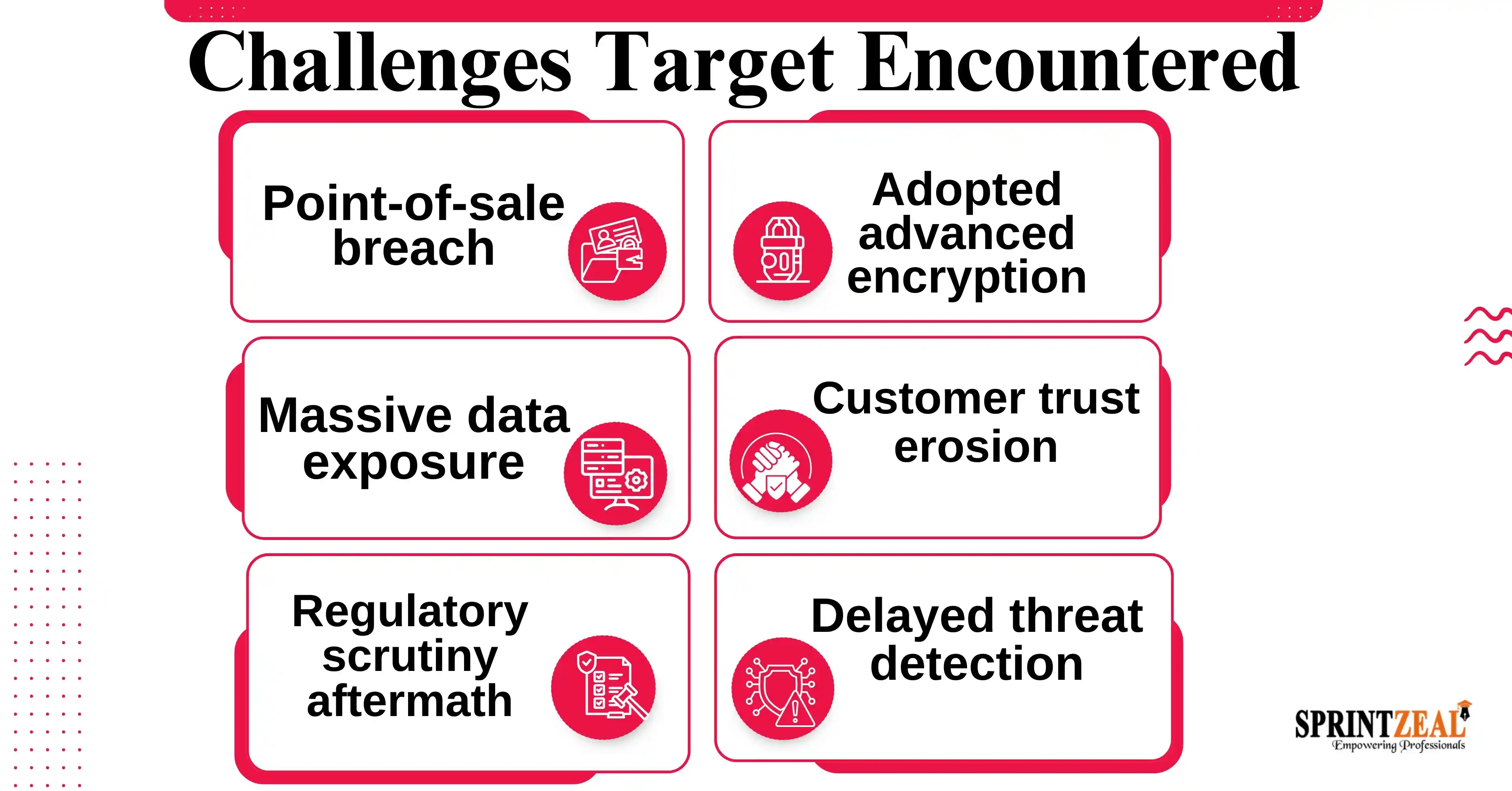
The Target cyber attack had far-reaching effects on the company or corporation, track record, and financial stability:
It takes advanced knowledge and expertise to comprehend and stop cyberthreats like the Target cyberattack. We at Sprintzeal provide recognized cybersecurity certification courses to keep professionals and companies ready. Our courses, taught by experts in the field, cover topics like risk assessment, vulnerability management, and advanced threat detection.
• Learn from case studies of actual events, like the Target cyberattack.
• Get hands-on expertise using creative tools and techniques.
• Set up yourself to protect your company from changing online threats.
The Target cyberattack acts as a reminder that cyber threats could indeed affect even players in the industry. The biggest businesses can enhance their defenses and protect themselves against comparable threats by taking a cue from Target's experience. Remaining ahead of cybercriminals requires proactive steps like strong third-party management, ongoing monitoring, and staff training.
What is a Target cyber attack?
Millions of customer credit and debit card details were made public in the 2013 Target cyberattack, a major data theft that tends to result from compromised third-party vendor credentials.
How did Target get hacked?
Credentials taken from a third-party HVAC vendor were used to hack Target. In order to obtain customer payment information, hackers got into Target's point-of-sale (POS) systems with fake software.
What is a targeted cyber attack example?
A targeted cyberattack is an intentional act that fits a specific system or organization. The 2013 Target data breach is a brilliant example of hackers invading a company through a seller to steal confidentiality.
What is a Target system in cyber security?
In cybersecurity, a target system refers to the network, software, or devices an attacker aims to exploit. For Target, it was their POS systems and customer databases.
Thu, 18 April 2024

Tue, 16 April 2024

Wed, 26 February 2025


© 2026 Sprintzeal Americas Inc. - All Rights Reserved.
Leave a comment