Why Become a Business Analyst in 2026: Top Reasons and Scope
Thu, 18 April 2024

Follow the stories of academics and their research expeditions

Each job within IT has a cybersecurity viewpoint. Concentrating on security as your essential job opens up a universe of choices. What’s more, don't let those negative features get you down.
For each Equifax, there are a huge number of effective exchanges made on the web. "Zero percent unemployment" is an alluring detail.
It's a decent advantage, without a doubt; however, it doesn't come close to a portion of the additional convincing process to seek a career in cybersecurity.
You don't necessarily have to be a cybersecurity master to comprehend that this is a growth area. As many ruptures hit the features, it's obvious to everybody that associations need more experts concentrated on cybersecurity.
Since the demand for cybersecurity professionals is strong, this could be the time where you can get your cybersecurity certification to uplift your career. A good certification can also provide you the advantage of seeking new opportunities.
Here are the five best reasons why you should get a cybersecurity certification.
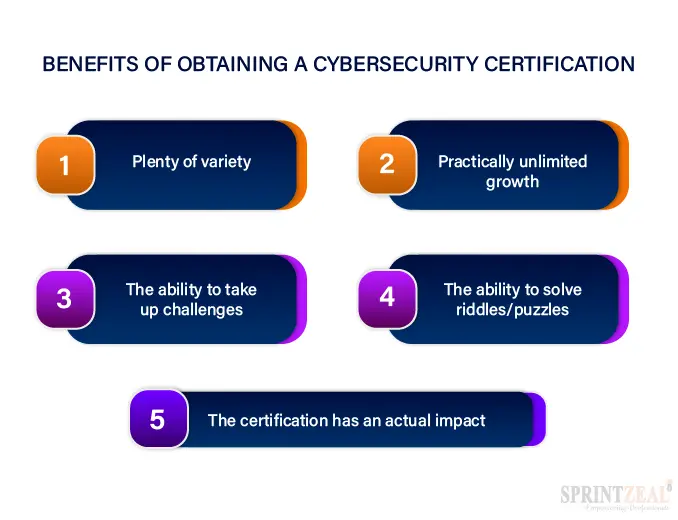
The entirety of the open doors for development is tied to the variety of technologies and situations security professionals have to deal with. On the off chance that it utilizes ones and zeros, it has a cybersecurity part (and a few jobs even reach out to physical security!).
Security experts find the opportunity to work straightforwardly with teams on technologies and systems they never longed for. From robots to vehicles to sites serving a great many clients, the variety is close to infinite.
The changes that constantly keep happening help you take advantage of the changes in the market and the field. A cybersecurity certification helps you have a secured career path.
With an ever-extending scope, cybersecurity presents an unlimited development potential—both in your career direction and for learning opportunities. We show security as its own order; still, it connects to the entirety of the other IT skills and abilities.
When you wisely close your cybersecurity certification level, there will be constant growth in your career options. Since cyber threats are on the rise, the growth in cyber security and the need for cybersecurity professionals is unstoppable.
Good cybersecurity proficiency attempts to understand as much as could be expected about how organizations and technology work. Extraordinary cybersecurity proficiency understands that there is no end to learning. That's a huge chance to remain determined and engaged.
At the point when security groups began, they began with "jack-of-all-trades" types. The control hadn't been sufficiently developed to help claims to support specialties in forensics, criminology, application security, or occurrence response.
Suggested Cybersecurity Course – CompTIA A+ Certification Course
The current workload has forced security groups to rapidly scale up and out. Opportunity is there for professionals ready to challenge themselves to take it.
Regardless of whether you're hoping to work your way towards a Chief Information Security Officer (CISO) job or to work with brand new technologies, the main thing that will confine your development is your desire.
That is an energizing recommendation and reason enough on its own to pick a profession in cybersecurity. Hence, a good cybersecurity certification can help you improve your skills in the IT field and uplift your career opportunities.
Include the development of innovation and its variety, and you begin to witness the various sorts of puzzles that cybersecurity experts can manage. In cybersecurity, we depend on some reliable standards, yet the strategies can change every day.
Furthermore, there's always another riddle that needs to be solved. With each new wave of innovation, new risks are expected. It's the duty of security experts to recognize, comprehend, and then help address these risks.
That changes essentially when you're thinking about how to protect a site running in the cloud contrasted with shielding a pacemaker in an old patient.
That last use case—guarding a pacemaker in an old patient—is a genuine one. Recently, there has been a massive review of pacemakers because of a security issue. The Equifax hack affected 145 million Americans.
Cybersecurity matters! It has impacts that stretch beyond the digital world and into the physical world. That is an alarming and energizing prospect, and one that features its significance. If at all you want to take a shot at IT jobs that have real-world impact, cybersecurity may be the field for you.
Suggested Resource – COBIT® Certification Training
A solid job showcase, great pay, steady challenges, and simplicity of section are just a couple of the compelling motivations to procure your certification and make the move into this rewarding and energizing profession.
In the field of IT professionals, there is no other corner that is as challenging as the cybersecurity profession. The cybersecurity certification also helps you identify the rightful choices to make and goals to remember and follow.
Regardless of whether you're working all day in another position, the move into this developing field can be made with the assistance of online digital security courses and certifications so you can achieve your objectives individually.
To know about the best cybersecurity courses, reach us at Click Here or chat with our course expert to get instant help finding the cybersecurity training that fits your career requirements the best.
Thu, 18 April 2024

Tue, 16 April 2024

Wed, 26 February 2025


© 2026 Sprintzeal Americas Inc. - All Rights Reserved.