5 Types of Cyber Attacks You Should Be Aware of in 2024
-
 By Niharika Chaurasia
By Niharika Chaurasia - Published on Aug 1 2023

Table of Contents
Introduction to Cyberattacks
Did you know that in 2024, what type of cyberattacks and data breaches peaked? Millions of people suffered as a result, and numerous organizations suffered huge monetary losses.
According to industry reports, 2024 witnessed a staggering surge in reported data breaches, with over 7 billion records exposed, marking a 93% increase from the previous year. The average cost of a data breach exceeded $4.24 million.
These data showed the essential need for people and organisations to be aware about and ready for changing cyber threats. Understanding the strategies used by cybercriminals can help us take preventative steps to safeguard our digital assets and ourselves.
In this guide, we unveil the top five types of cyber-attacks that dominated 2024. From phishing and ransomware to insider threats and IoT vulnerabilities, we will explore why cyber-attacks are rising, understanding of cybersecurity fundamentals and details of each attack. Also, how you can strengthen cyber defense.
The Rise of Cyber Threats
Cyber threats have reached alarming levels, posing significant risks worldwide. Since there is rapid advancement in technology, it enables an easy gateway for sophisticated cybercriminals to exploit vulnerabilities for financial gain, data breaches, and disruption.
Key factors contributing to the rise of cyber threats include:
-Proliferation of connected devices, IoT, and cloud computing expands the attack surface, offering more opportunities for cybercriminals.
-Emerging technologies like AI and machine learning are exploited by threat actors to develop sophisticated attack techniques.
-Widespread internet adoption interconnects individuals and organizations, providing more targets for cybercriminals.
-Rise of remote work and digital transformation amplifies risk as people access corporate networks from different devices and locations.
-Through activities like ransomware and identity theft, cybercrime is highly beneficial and gives financial gains to the attackers.
-Cryptocurrencies facilitate anonymous transactions, making it easier for cybercriminals to monetize their activities.
-Humans remain the weakest link in cybersecurity, vulnerable to social engineering techniques like phishing.
-Addressing these factors and implementing robust cybersecurity measures is crucial in mitigating cyber threats.
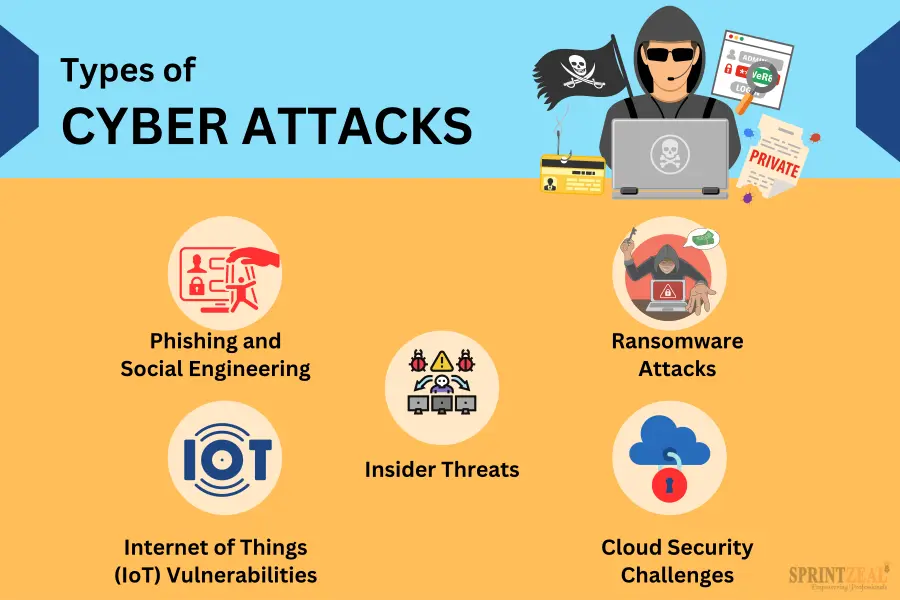
Top 5 Types of Cyber Attacks
Here are the top 5 types of cyber attacks which put organizations and systems at risk. Its essential to understand there threats and implement robust security measures to mitigate these threats.
Phishing and Social Engineering: Hook, Line, and Sinker
Phishing and social engineering remain popular and effective tactics employed by cybercriminals to deceive and gain unauthorized access to sensitive information. In 2024, over 80% of reported cyber incidents involved phishing attacks, demonstrating their widespread use and success.
Phishing attacks often take the form of deceptive emails, texts, or instant messages that mimic trusted sources. These cunning messages trick recipients into sharing confidential data like passwords, credit card details, or login credentials. Social engineering techniques exploit human psychology, manipulating individuals into compromising their security.
Cybercriminals constantly refine their phishing methods, making it increasingly difficult to differentiate between genuine and malicious communication. To defend against phishing attacks, it's vital to remain vigilant, verify requests, avoid clicking suspicious links or downloading attachments, and keep security software up to date.
Ransomware Attacks: Holding Your Digital World Hostage
Ransomware attacks pose a grave cybersecurity threat, causing massive damage and financial losses. In 2024, reported incidents surged by over 50%, underscoring the growing danger. Attackers employ phishing emails, exploit kits, and vulnerable protocols to distribute malware that encrypts files, demanding a ransom for their release.
Victims face dire consequences, impacting individuals, businesses, and critical infrastructure. Ransom demands can reach millions. To mitigate risk, regularly back up data, implement robust cybersecurity measures, educate employees on phishing, segment networks, and develop an incident response plan.
Insider Threats: The Enemy Within
While external threats receive significant attention, organizations also face risks from within their own ranks. Insider threats, whether intentional or accidental, can result in significant data breaches and financial losses. In fact, studies show that insider incidents account for nearly 30% of data breaches.
Insiders with authorized access to sensitive information can abuse their privileges, intentionally leak data, or engage in malicious activities. Additionally, accidental insider incidents can occur due to human error or negligence, such as employees mishandling data or falling victim to social engineering.
Preventing insider threats requires a comprehensive approach that includes implementing strict access controls, monitoring employee behavior, conducting thorough background checks, and providing regular cybersecurity training. Organization can effectively mitigate the risks posed by insider threats and protect their valuable assets by adopting a culture of security and promoting employee awareness.
Internet of Things (IoT) Vulnerabilities: Bridging the Gap
The increased use of Internet of things brings new challenges for cybersecurity. Interconnected devices like smart home appliances or industrial control systems often lack sufficient security protections, making them vulnerable to cyberattacks.
Exploiting IoT flaws can result in serious repercussions, such as unauthorized access to private information, the disruption of vital infrastructure, and even physical injury. To take over IoT devices, hackers use obsolete software, unsecured connections, and weak passwords.
To bridge the gap and bolster IoT security, it is crucial for manufacturers to prioritize security during the design and development phase. This involves implementing strong encryption, regular software updates, and robust authentication mechanisms.
Users also play a vital role by practicing good IoT hygiene, such as changing default passwords, securing Wi-Fi networks, and staying vigilant against suspicious activities.
Cloud Security Challenges: Navigating the Skies
Business operations have changed as a result of the use of cloud computing, which provides scalability, flexibility, and cost-efficiency. It also presents certain security difficulties, though. The huge amount of sensitive data kept in cloud settings makes them ideal targets for attacks.
Organisations face a variety of cloud security challenges, including risks for data loss, unauthorised access, and setup errors. Strong access controls, encryption, regular vulnerability assessments, and checking for unusual activity are all necessary for ensuring reliable cloud security.
Businesses may use the cloud's capabilities while protecting their data by being aware of these problems and implementing strong security procedures. To keep a safe and robust digital infrastructure, organisations should place a high focus on cloud security.
How to Strengthen Your Cyber Defense?
When it comes to defending against cyber threats, there are several key areas to focus on. Let's explore some effective strategies to bolster your cyber defense:

Network Security
To protect your digital assets, it's essential to build a strong network security infrastructure. Firewalls, intrusion detection systems, and virtual private networks (VPNs) must all be put into place in order to do this. You can identify and stop unauthorised actions by establishing a secure network architecture, putting access rules in place, and keeping an eye on network activity.
Security Awareness and Training
Human error remains one of the weakest links in cybersecurity. We'll emphasize the importance of security awareness and training programs in creating a cyber-resilient culture. From educating employees about common threats to conducting simulated phishing exercises, you'll discover strategies for fostering a security-conscious workforce.
Endpoint Security
Endpoints, including laptops, smartphones, and IoT devices, are often the first line of defense against cyber threats. Strengthening endpoint security is crucial. Implementing strong passwords, using encryption, and keeping software up to date are essential practices for securing your devices. By fortifying your endpoints, you can significantly reduce the risk of compromise
Data Encryption
Encryption plays a vital role in protecting sensitive data, whether it's at rest or in transit. Understanding how encryption works and implementing it effectively is critical. Learn about different encryption algorithms, ensure proper key management, and follow best practices for encryption implementation within your organization.
Sprintzeal's Cybersecurity Training Programs
Gear up for an exciting cybersecurity journey with Sprintzeal! Discover our range of industry-leading cybersecurity courses and certifications designed to equip you with the skills and knowledge needed to thrive in the cybersecurity landscape. From Certified Information Systems Security Professional (CISSP) to Certified Cloud Security Professional (CCSP), we've got you covered.
Why Choose Sprintzeal?
Explore the benefits of learning with Sprintzeal, including expert instructors, hands-on learning experiences, flexible learning options, and globally recognized certifications. Don't miss the chance to boost your cybersecurity career with our comprehensive training programs.
Conclusion
Cyber dangers are an increasing worry for people and businesses in today's digital world. In order to safeguard ourselves and our digital assets, it is crucial to be aware of the top cyber risks in 2024 and take preventative action. By embracing cybersecurity practices, staying vigilant against social engineering, and prioritizing awareness, we can effectively combat these threats.
Sprintzeal is here to support your cybersecurity journey. With comprehensive training courses and expert instructors, we equip you with the knowledge and skills to navigate the ever-changing cybersecurity landscape. Enroll with Sprintzeal today and become a cyber warrior making a difference in the fight against cybercrime.
Let's stay ahead of hackers and safeguard our digital world.
Subscribe to our Newsletters
Popular Programs
CISSP® - Certified Information System Security Professional
Live Virtual Training
- 4.1 (964 + Ratings)
- 30k + Learners
CISA® - Certified Information System Auditor
Live Virtual Training
- 4.8 (426 + Ratings)
- 31k + Learners
CISM® - Certified Information Security Manager
Live Virtual Training
- 4.8 (200 + Ratings)
- 52k + Learners
CCSP® - Certified Cloud Security Professional
Live Virtual Training
- 4.7 (964 + Ratings)
- 25k + Learners
Trending Posts
How Target Turned a Cyber Crisis into a Lesson for All
Last updated on Jan 2 2025
Cybersecurity Roles - Top Roles and Skills to Consider in 2024
Last updated on Mar 6 2023
Risk-based Audit Planning Guide for Beginners
Last updated on Dec 6 2023
Cybersecurity Mesh: A New Approach for Security Design
Last updated on Jan 3 2025
Risk-Based Internal Auditing Approaches: 7 Steps to Explore
Last updated on Dec 20 2023
What is a Cybersecurity Incident?-Types, Impact, Response Process and More
Last updated on Jul 18 2023
Categories
- Agile Management 54
- AI and Machine Learning 42
- Big Data 53
- Business Management 51
- Cloud Computing 44
- Digital Marketing 56
- Information Security 8
- IT Hardware and Networking 17
- IT Security 103
- IT Service Management 29
- Leadership and Management 1
- Microsoft Program 2
- Other 43
- Programming Language 31
- Project Management 162
- Quality Management 75
- Risk Management 8
- Workplace Skill Building 2
Trending Now
Which Certification is best for Cybersecurity?
ebookTop 5 Compelling Reasons To Get A Cyber Security Certification
ebookHow to Become IT Security Expert with CISSP Certification
ebookTop 20 Reasons You Should Get a CISSP Certification
ebookCISM certification cost and career benefits
ebookWhat is CISSP? – Everything about CISSP Certification Explained
ebookPass CISSP Exam - How to Clear CISSP Exam in First Attempt 2024 (UPDATED)
ebookCISSP Certification – Top 25 Career Benefits in 2024
ebookCybersecurity – Everything You Need to Know About it
ebookCybersecurity Strategy: Building a Strong Defense for Business
ebookCyber Attack Statistics and Trends to Know in 2024
ebookUpdated Google Certification Training Course list 2024
ArticleWhich Cybersecurity Certification Should I Get First?
ebookCysa+ certification – Should you get it?
ebookList of Top Security Certifications
ArticleEasiest Security Certification to Get
ebookCybersecurity Fundamentals Explained
ebookISACA Certifications List 2024
ebookCareer Benefits of CISM Certification in 2024
ArticleList of Top Information Security Certifications in 2024
ebookCISM certification cost details
ArticleSafeguarding Digital Domain: 10 Most Common Cybercrimes
ebookMitigate the Cyber-Attack Risks with Best Cyber Security Protocols
ebookCybersecurity Interview Questions and Answers 2024
ebookData Leak - What is it, Prevention and Solutions
ebookTop Cybersecurity Software Tools In 2024
ebookWhat is Cryptography - A Comprehensive Guide
ebookInformation Security Analyst - Career, Job Role, and Top Certifications
ebookCyber Security Analyst - How to Become, Job Demand and Top Certifications
ebookIBM Data Breach: Is IBM Really Breach-Proof?
ArticleWhat is the Department of Defense (DoD) Directive 8140
ebookInformation Assurance Model in Cybersecurity
ebookWhat is Data Security - Types, Strategy, Compliance and Regulations
ebookData loss Prevention in Cyber Security Explained
ebookCybersecurity Controls Explained in Detail
ebookCybersecurity Framework - A Complete Guide
ebookCybersecurity Career Paths Guide
ebookFuture of Cybersecurity - Trends and Scope
ebookScope for Cybersecurity in 2024 - Update for 2024
ebookCyber Security Careers and Outlook - 2024 Guide
ebook5 Cybersecurity Predictions in 2024 - Trends and Challenges
ebookEthical Hacking Career: A Career Guide for Ethical Hacker
ebookApplication Security: All You Need To Know
ebookCybersecurity Roles - Top Roles and Skills to Consider in 2024
ebookHow to Get Cyber Essentials Certified
ebookTop 10 Cyber Security Threats and How to Prevent Them
ebookTop 10 Network Scanning Tools of 2025
ebookCyber Incident Response Plan: A Comprehensive Guide
ebookInformation Assurance Careers - Exploring Career Paths
ebookCybersecurity Mesh Architecture: What It Is and How to Build It
ebookWhat is Threat Modeling? Methodologies, Types, and Steps
ebookWhat is Digital Forensics? Types, Process & Challenges
ebookRecent Cyber Attacks & Data Breaches in 2024
ebookHow to Become an Information Security Analyst Salary, Skills, and More
ArticleList of Top Department of Defense (DoD) Approved 8570 Certification Courses
ebookTop 5 Ransomware Attacks to Watch Out for in 2024
ebookJob Prospects for DoD Certified Professionals: A Pathway to Success in cybersecurity
ebook10 Biggest Data Breaches of the 21st Century
ebookWhat is a Cybersecurity Incident?-Types, Impact, Response Process and More
ebookCyber Security Planning - A Detailed Guide for Risk Mitigation
ebookWhat is Cybercrime? Exploring Types, Examples, and Prevention
ebookCybercrime Impacts On Business: 6 Major Effects
ebookCloud Cyber Attacks: Causes, Types, Prevention and Protection
ebookCloud Malware: Types of Attacks and Security Measure
ebookList Of Top Cybersecurity Threats In 2024
ebookRisk-based Audit Planning Guide for Beginners
ebookDemystifying Cloud-Based Cyber Attacks: A Comprehensive Guide
ebookPrevent Cyber Attacks: Strategies to Protect Your Digital Assets
ebookList of Top 10 Cybersecurity Careers in 2024
ebookTop 20 Cybersecurity Trends to Watch Out for in 2024
ArticleHow to Become Cybersecurity Engineer
ArticleUnderstanding Risk assessment in audit planning
ArticleFundamentals of Risk-Based Auditing: A Strategic Framework
ArticleTop 8 Types of Cybersecurity Jobs and Salary Insights
ArticleA Comprehensive Guide to Building Risk-Based Internal Audit Plan
ArticleRisk-Based Internal Auditing Approaches: 7 Steps to Explore
ArticleCompTIA Security+ 601 vs. 701: Understanding Key Differences
ArticleWhy and How to Perform a Risk-Based Internal Audit
ArticleRisk-Based Auditing Techniques Explained
ebookEthical Hacking Tools: Best Ones for Cybersecurity in 2025
ArticleEvolving Cyber Threats and Vulnerabilities in Cybersecurity Risk Management
ArticleWhat Is Secure Access Service Edge (SASE)?
ArticleHow to Stay Cyber-Secure in Work and Personal Life (Tips and Practices)
ArticleTarget Cyber Attack: Key Lessons from the 2013 Data Breach
ArticleLinkedIn User Data Protection Explained
ArticleCanva Data Breach: Best Lessons for Users and Businesses
ArticleHow Did Capital One Respond to Their Major Cyber Incident?
ArticleWhat Innovative Measures Did Reddit Take to Protect User Data?
ArticleHow Does Slack Respond to Security Challenges?
ArticleTwitch Data Breach: Response, Changes, and Key Takeaways
ArticleGuess What Google Did When a Employee Breached Their Firmware
ArticleWhat Happened When Cisco Faced a Cyber Incident?
ArticleWhat Sony Did to Rebuild Trust After a Major Cyberattack
ArticleHow to Handle a Data Breach? Learn from Microsoft!
ArticleCybersecurity Mesh: A New Approach for Security Design
ArticleHow Target Turned a Cyber Crisis into a Lesson for All
ArticleDropbox Data Breach: What Companies Can Learn from It
ArticleHow JPMorgan Chase Strengthened Security After Facing Cyber Threats
ArticleThe Future of Online Security: Trends to Watch in 2025
ArticleLatest Trends in CyberSecurity
ArticleTop 12 Cyber Security Apprenticeships with High Earning Potential in 2025
ArticleEnhancing Safety and Competence in Today's Workplace
Article
















